To choose the right penetration testing service provider, assess their certifications and experience in the industry. Evaluate their methodologies and tools to ensure they align with your specific security needs.
How to Choose the Right Penetration Testing Service:Selecting a penetration testing service provider is crucial for safeguarding your organization’s sensitive data. Cyber threats continue to evolve, making it essential to partner with experts who understand the latest vulnerabilities. An effective provider not only identifies weaknesses but also offers actionable insights to strengthen your defenses.
By understanding your unique requirements and evaluating potential partners carefully, you can enhance your security posture. This guide will help you navigate the selection process, ensuring that you choose a provider that meets your technical needs and aligns with your budget. Prioritize transparency, communication, and proven results in your search for the right partner.
Introduction To Penetration Testing
Penetration testing is a crucial part of cybersecurity. It helps organizations identify weaknesses in their systems. This proactive approach protects sensitive data from cyber threats. Understanding penetration testing is essential for choosing the right service provider.
The Importance Of Cybersecurity
Cybersecurity is vital for every organization. It safeguards data, reputation, and customer trust. Here are some key reasons why cybersecurity matters:
- Data Protection: Keeps sensitive information safe from breaches.
- Regulatory Compliance: Meets legal requirements to avoid penalties.
- Business Continuity: Ensures operations run smoothly during an attack.
- Reputation Management: Maintains a positive image in the market.
Role Of Penetration Testing In Security
Penetration testing simulates attacks on systems. This helps find vulnerabilities before hackers do. Here are its primary roles:
- Identify Vulnerabilities: Discover weaknesses in applications and networks.
- Test Security Measures: Evaluate the effectiveness of current defenses.
- Improve Response Plans: Enhance incident response strategies.
- Educate Staff: Raise awareness about potential cyber threats.
Penetration testing is essential for a robust security strategy. Choosing the right service provider enhances your overall security posture.
Types Of Penetration Testing Services
Choosing the right penetration testing service provider involves understanding different types of services. Each type targets specific areas of your network or application. Knowing these types helps you make an informed decision.
External Network Testing
External Network Testing checks your network from outside. This type simulates attacks from hackers on the internet. It focuses on:
- Firewalls
- Routers
- Public IP addresses
Important goals include:
- Identifying vulnerabilities.
- Assessing firewall rules.
- Testing security controls.
Internal Network Testing
Internal Network Testing examines your network from inside. This type mimics threats from users within the organization. Key aspects include:
- Identifying insider threats.
- Assessing internal security measures.
- Testing employee access controls.
Benefits include:
- Uncovering weaknesses.
- Improving incident response.
- Strengthening overall security.
Web Application Testing
Web Application Testing targets your websites and web apps. This type checks for common vulnerabilities. It focuses on:
- SQL Injection
- Cross-Site Scripting (XSS)
- Authentication flaws
Key objectives include:
- Ensuring data protection.
- Validating user input.
- Enhancing application security.
Social Engineering Tests
Social Engineering Tests assess human factors in security. This type simulates real-world attacks like phishing. It focuses on:
- Employee awareness
- Response to suspicious emails
- Access control breaches
Goals include:
- Raising security awareness.
- Testing incident response.
- Identifying training needs.
Setting Your Security Goals
Choosing the right penetration testing service provider begins with clear security goals. Understanding what you want to protect is crucial. This helps in selecting the best provider for your needs.
Identifying Assets And Potential Threats
Start by listing your key assets. These can include:
- Customer data
- Intellectual property
- Financial information
- Critical infrastructure
Next, identify potential threats to these assets:
| Asset | Potential Threat |
|---|---|
| Customer Data | Data Breaches |
| Intellectual Property | Industrial Espionage |
| Financial Information | Fraud |
| Critical Infrastructure | Cyber Attacks |
Understanding these factors helps shape your security strategy. A clear picture of what you need to protect guides your choice.
Defining The Scope Of Penetration Testing
The scope outlines what areas to test. A well-defined scope is vital for effective penetration testing.
Consider these questions:
- What systems need testing?
- Which networks are in scope?
- What types of tests are required?
Examples of testing types include:
- External network tests
- Internal network tests
- Web application tests
- Social engineering tests
Clearly defining the scope ensures the testing aligns with your security goals. This helps in identifying vulnerabilities effectively.

Credit: teceze.com
Criteria For Choosing A Pen Test Service
Choosing the right penetration testing service is essential for security. Consider several criteria to ensure the provider meets your needs. Focus on their experience, methodologies, compliance, and communication skills.
Experience And Expertise
Experience is crucial in penetration testing. A provider with a strong track record is more reliable. Look for the following:
- Years in business: More years often mean more knowledge.
- Certifications: Check for certifications like CEH, OSCP, or CISSP.
- Industry experience: Ensure they have worked in your specific industry.
Methodologies And Tools Used
Different providers use various methodologies and tools. Ensure they align with your security needs. Key aspects to consider include:
| Methodology | Description |
|---|---|
| OWASP | Focuses on web application security. |
| NIST | Government standard for testing and assessment. |
| PTES | Comprehensive testing framework. |
Inquire about the tools they use. Popular tools include:
- Nmap: Network scanning tool.
- Burp Suite: Web application testing tool.
- Metasploit: Penetration testing framework.
Compliance And Industry Standards
Compliance with industry standards is vital. Different sectors have specific regulations. Check for:
- PCI-DSS: For payment card security.
- HIPAA: For healthcare data protection.
- GDPR: For data privacy in the EU.
Ensure the provider understands these standards. They should help you meet compliance requirements.
Reporting And Communication
Effective reporting and communication are essential. A good provider should offer:
- Clear reports: Easy-to-understand findings.
- Actionable recommendations: Steps to fix vulnerabilities.
- Regular updates: Keep you informed during testing.
Ask about their communication style. Regular updates build trust and transparency.
Understanding Penetration Testing Certifications
Choosing the right penetration testing service provider is crucial. Certifications indicate expertise and knowledge in the field. They help ensure that you hire skilled professionals. Understanding these certifications will guide your decision.
Certified Ethical Hacker (ceh)
The Certified Ethical Hacker (CEH) certification is popular. It focuses on ethical hacking techniques. CEH professionals learn to think like attackers. This helps them find vulnerabilities in systems.
- Focus on ethical hacking methods.
- Covers various hacking tools and techniques.
- Recognized globally in cybersecurity.
Licensed Penetration Tester (lpt)
The Licensed Penetration Tester (LPT) certification is advanced. It is for experts in penetration testing. LPT focuses on real-world scenarios. This certification proves deep knowledge and skills.
- Requires completion of practical exams.
- Emphasizes advanced testing methodologies.
- Recognized by top organizations in cybersecurity.
Offensive Security Certified Professional (oscp)
The Offensive Security Certified Professional (OSCP) certification is highly respected. It emphasizes hands-on experience. OSCP candidates must complete a challenging exam. This tests practical skills in real environments.
- Focuses on practical penetration testing.
- Includes a rigorous exam with real challenges.
- Highly regarded by employers in cybersecurity.
| Certification | Focus Area | Recognition |
|---|---|---|
| CEH | Ethical Hacking Techniques | Global |
| LPT | Advanced Penetration Testing | Top Organizations |
| OSCP | Hands-on Practical Skills | Highly Respected |
Credit: www.blazeinfosec.com
The Role Of Automated Tools Vs. Human Expertise
Choosing the right penetration testing service is crucial. Understanding the balance between automated tools and human expertise is key. Both have unique strengths. Knowing when to use each can enhance security efforts.
Benefits Of Automated Penetration Testing
Automated tools offer several advantages:
- Speed: Automated tools can scan systems quickly.
- Cost-Effective: Automation reduces labor costs.
- Consistency: Tools provide uniform results every time.
- Coverage: They can test many systems simultaneously.
These benefits make automated testing a popular choice for many organizations. It helps identify common vulnerabilities efficiently.
Limitations Of Automation
Despite their benefits, automated tools have limitations:
- False Positives: Tools may flag issues that aren’t real.
- Context Ignorance: Tools can’t understand the environment fully.
- Complex Scenarios: Advanced attacks may go undetected.
Relying solely on automation can leave gaps in security. Understanding these limitations is essential.
When To Rely On Human Expertise
Human expertise is crucial in several situations:
- Complex Systems: Complex environments need human insight.
- Custom Applications: Unique applications require tailored testing.
- Advanced Threats: Sophisticated attacks need human analysis.
- Policy Compliance: Compliance requires human judgment and interpretation.
Humans can analyze results and provide context. They understand security nuances that tools may miss. Combining both methods enhances overall security posture.
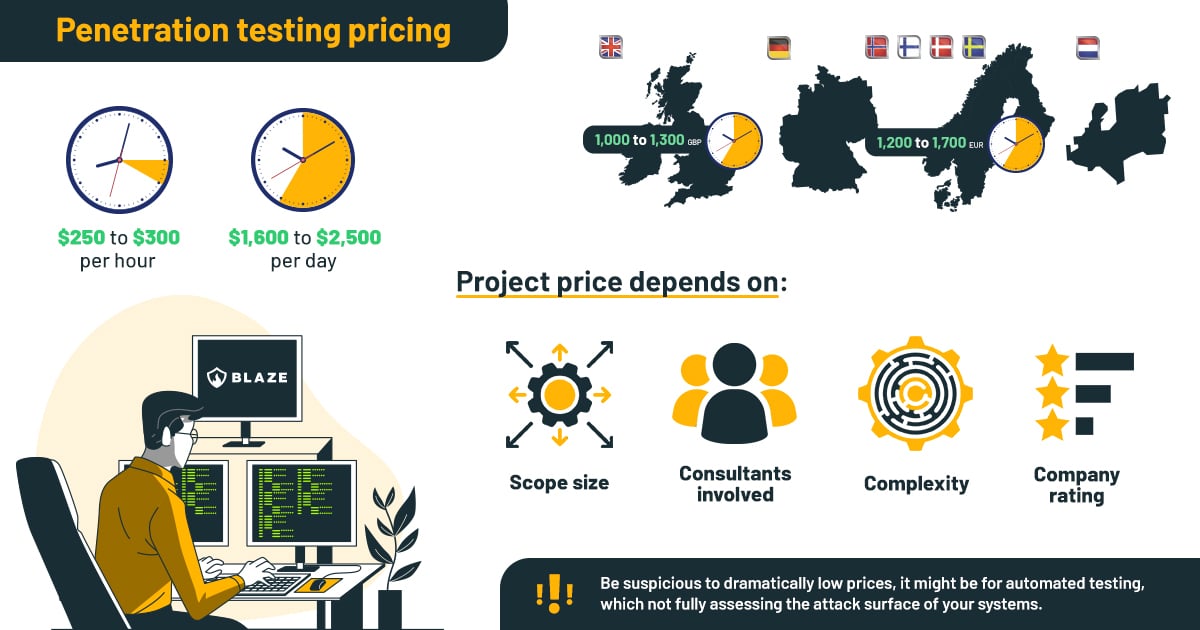
Budgeting For Penetration Testing Services
Choosing the right penetration testing service provider involves careful budgeting. Understanding costs helps you make informed decisions. A clear budget ensures quality testing without overspending. Here are key factors to consider.
Cost Factors In Penetration Testing
Several factors influence the cost of penetration testing services:
- Scope of Testing: Larger networks cost more to test.
- Type of Test: Black box, white box, or gray box tests have different prices.
- Experience Level: Experts charge higher fees for their skills.
- Location: Providers in different regions may have varying rates.
| Cost Factor | Average Cost Range |
|---|---|
| Basic Network Test | $1,000 – $5,000 |
| Web Application Test | $3,000 – $10,000 |
| Comprehensive Test | $10,000 – $30,000 |
Balancing Cost And Quality Of Service
Cost should not be the only factor in your decision. Quality is essential for effective penetration testing.
- Read Reviews: Look for customer feedback on providers.
- Check Certifications: Certified professionals offer better quality.
- Request Proposals: Compare costs and services from multiple providers.
Choose a provider that meets your budget while ensuring quality. Skimping on security can lead to bigger losses later.
Engaging With A Penetration Testing Provider
Choosing the right penetration testing provider is crucial. The engagement process sets the stage for a successful assessment. It involves clear communication and understanding your needs.
Initial Consultation And Assessment
The first step is the initial consultation. This is where you discuss your specific requirements. A good provider will:
- Ask about your security goals.
- Evaluate your current security posture.
- Suggest the type of penetration test needed.
During this assessment, be prepared to share:
- Details about your network architecture.
- Your compliance requirements.
- Any previous security incidents.
Effective communication during this phase builds trust. It ensures the provider understands your expectations.
Contract And Engagement Terms
The contract outlines the scope of work. It should clearly define:
| Aspect | Details |
|---|---|
| Scope of Testing | What systems and applications will be tested? |
| Timeline | Start and end dates for the testing. |
| Payment Terms | Cost and payment schedule. |
Review all terms carefully. Make sure all parties agree on expectations. Clarity prevents misunderstandings down the line.
Post-testing Support And Remediation
After the penetration test, support is crucial. A reliable provider offers:
- Detailed reports of findings.
- Recommendations for remediation.
- Follow-up consultations.
This ongoing support helps you understand vulnerabilities. Implementing recommendations strengthens your security posture.
Always ask about the provider’s approach to remediation. Ensure they are available for questions and guidance.
Evaluating And Acting On Test Results
Evaluating and acting on penetration testing results is crucial. It helps organizations understand their security posture. Proper analysis leads to effective remediation. Businesses must interpret findings, prioritize vulnerabilities, and implement continuous improvement strategies.
Interpreting The Report Findings
Understanding the penetration testing report is essential. Key aspects include:
- Executive Summary: A high-level overview of findings.
- Technical Details: Specific vulnerabilities and their implications.
- Recommendations: Suggested actions for remediation.
Focus on the critical vulnerabilities first. Identify vulnerabilities categorized as high, medium, or low risk. Use the following table for clarity:
| Risk Level | Description | Action Required |
|---|---|---|
| High | Immediate threat to data security. | Remediate within 24 hours. |
| Medium | Potential risk but not immediate. | Address within one week. |
| Low | Minor vulnerabilities. | Fix at next maintenance window. |
Prioritizing Vulnerabilities For Remediation
Not all vulnerabilities require immediate attention. Prioritization is key for effective remediation. Consider the following factors:
- Impact: How severe is the risk?
- Exploitability: How easy is it for attackers to exploit?
- Business Context: What is the importance of the affected system?
Focus first on high-risk vulnerabilities. This approach minimizes potential damage. Use a risk matrix to visualize priorities:
| Risk Level | Immediate Action | Follow-Up Action |
|---|---|---|
| High | Fix immediately. | Monitor system closely. |
| Medium | Schedule for remediation. | Assess for further risks. |
| Low | Document and track. | Review regularly. |
Continuous Improvement And Re-testing
Security is an ongoing process. Regularly re-test systems after remediation. Continuous improvement helps maintain security posture. Implement a schedule for periodic testing:
- Quarterly assessments for critical systems.
- Annual tests for less critical systems.
Incorporate lessons learned into security policies. This proactive approach strengthens defenses. Build a culture of security awareness within the organization. Engage all employees in security best practices.
Credit: www.cobalt.io
Frequently Asked Questions
What Should I Look For In A Provider?
When selecting a penetration testing service provider, consider their experience and expertise. Look for certifications like OSCP or CEH. Evaluate their methodologies and tools used. Review client testimonials and case studies. Ensure they offer tailored solutions to meet your specific security needs.
How Do I Assess A Provider’s Expertise?
To assess a provider’s expertise, check their qualifications and certifications. Look for industry-recognized accreditations. Review their past projects and client feedback. Ask for references and case studies. Inquire about their team’s ongoing training and development in cybersecurity.
What Types Of Penetration Testing Services Are Available?
Penetration testing services include network, web application, and mobile application testing. Additionally, some providers offer social engineering and physical security assessments. Choose based on your organization’s specific vulnerabilities. Tailored services can better meet your security requirements.
How Much Do Penetration Testing Services Cost?
The cost of penetration testing services varies widely. Factors include the scope of the test, provider expertise, and the complexity of your systems. Generally, prices range from a few thousand to tens of thousands of dollars. Always request a detailed quote outlining services included.
Conclusion
Choosing the right penetration testing service provider is crucial for your organization’s security. Assess their expertise, tools, and methodologies carefully. Verify their track record and client feedback to ensure reliability. A well-chosen provider will help safeguard your assets and enhance your security posture.
Make an informed decision to protect your digital environment.





Leave a Reply