To secure API endpoints in modern web applications, implement authentication and authorization mechanisms. Use HTTPS to encrypt data in transit and protect against man-in-the-middle attacks.
How to Secure API Endpoints:APIs play a crucial role in modern web applications, facilitating data exchange and enabling seamless user experiences. As their usage grows, so do the risks associated with API security. Cyber threats like data breaches and unauthorized access can lead to significant consequences for businesses and users alike.
Therefore, securing API endpoints is essential for safeguarding sensitive information and maintaining user trust. Employing best practices in API security not only protects your application but also enhances its overall integrity. This guide delves into effective strategies for securing API endpoints, ensuring robust protection against potential vulnerabilities.
Introduction To Api Security
APIs are vital for modern web applications. They connect different services and share data. However, they also open doors to potential threats. Securing API endpoints is crucial. This ensures data stays safe from unauthorized access.
The Rise Of Api Usage
APIs have become essential in today’s digital world. Businesses rely on them for various functions.
- Data exchange between applications
- Integration of third-party services
- Mobile app functionality
- Automation of processes
With the increase in API usage, security risks also grow. Developers must prioritize API security to protect data and services.
Potential Risks Involved
APIs can expose applications to several risks. Understanding these risks helps in implementing better security measures.
| Risk Type | Description |
|---|---|
| Data Breaches | Unauthorized access to sensitive information. |
| Injection Attacks | Malicious code injected into API requests. |
| DDoS Attacks | Overloading the API with excessive requests. |
| Insufficient Authentication | Weak verification of user identities. |
Developers must recognize these risks. Taking proactive steps can mitigate these threats. Regular security audits and updates are key.

Credit: brightsec.com
Identifying Vulnerable Api Endpoints
Identifying vulnerable API endpoints is crucial for web application security. Attackers often target these endpoints to exploit weaknesses. Understanding common flaws helps developers fortify their applications. This section covers common API security flaws and tools for vulnerability assessment.
Common Api Security Flaws
API endpoints can have various security flaws. Here are some of the most common:
- Broken Authentication: Weak or missing authentication checks.
- Excessive Data Exposure: APIs reveal more data than necessary.
- Rate Limiting Issues: Lack of limits on requests allows abuse.
- Injection Attacks: Attackers inject malicious code through inputs.
- Security Misconfigurations: Default settings can lead to vulnerabilities.
Tools For Vulnerability Assessment
Several tools can help identify vulnerabilities in API endpoints. Here are some effective options:
| Tool Name | Description |
|---|---|
| Postman | API testing tool with automated security checks. |
| OWASP ZAP | Open-source tool for finding security vulnerabilities. |
| Burp Suite | Comprehensive tool for web application security testing. |
| SoapUI | API testing tool with security scan features. |
Using these tools can greatly improve your API security. Regular assessments help catch vulnerabilities early.
Authentication And Authorization Strategies
Securing API endpoints is crucial for modern web applications. Two key concepts help protect these endpoints: authentication and authorization. Authentication verifies the identity of users. Authorization determines what users can do. Using robust strategies is essential for keeping data safe.
Implementing Oauth 2.0
OAuth 2.0 is a widely-used framework. It allows third-party applications to access user data without sharing passwords. Here’s how to implement it:
- Register your application with the OAuth provider.
- Obtain client credentials. This includes a client ID and secret.
- Redirect users to the OAuth provider for authentication.
- Receive authorization code after user consent.
- Exchange the code for an access token.
The access token allows your application to interact with user data. It’s essential to:
- Store tokens securely.
- Set expiration times to limit access.
- Refresh tokens when necessary.
Utilizing Api Keys Effectively
API keys are simple and effective. They help identify and authenticate users. Here’s how to use them:
| Best Practices for API Keys | Description |
|---|---|
| Keep keys secret | Never expose API keys in public code. |
| Use environment variables | Store keys in server settings, not in code. |
| Regenerate keys regularly | Change keys to minimize risk. |
| Monitor usage | Track API key activity for unusual behavior. |
By following these strategies, you can enhance the security of your API endpoints. Protecting user data is crucial in today’s digital landscape.
Encryption Techniques For Data Protection
Securing API endpoints is crucial for modern web applications. Encryption protects sensitive data from unauthorized access. Implementing strong encryption methods ensures data integrity and privacy.
Ssl/tls For Data Transit
Using SSL (Secure Sockets Layer) and TLS (Transport Layer Security) is essential for encrypting data in transit. This protects data exchanged between clients and servers.
Key benefits of SSL/TLS include:
- Confidentiality: Keeps data hidden from eavesdroppers.
- Integrity: Ensures data is not altered during transit.
- Authentication: Confirms the identity of the communicating parties.
Implementing SSL/TLS involves:
- Obtaining a valid SSL/TLS certificate.
- Configuring your server to use HTTPS.
- Redirecting all HTTP traffic to HTTPS.
At-rest Encryption Best Practices
At-rest encryption secures data stored on servers. It protects data from unauthorized access, even if physical security is compromised.
Follow these best practices for at-rest encryption:
- Use strong encryption algorithms like AES-256.
- Encrypt sensitive data only, such as personal information.
- Manage encryption keys securely.
Consider this simple table for encryption methods:
| Method | Description | Use Case |
|---|---|---|
| AES-256 | Advanced Encryption Standard with 256-bit key. | Encrypt sensitive files. |
| RSA | Asymmetric encryption for secure key exchange. | Secure API authentication. |
| Blowfish | Fast block cipher encryption. | Encrypting database records. |
Implementing these encryption techniques enhances the security of your web applications. Protecting data both in transit and at rest is vital for safeguarding user information.
Input Validation And Sanitization
Input validation and sanitization are crucial for securing API endpoints. They help prevent harmful data from entering your application. Malicious users often exploit vulnerabilities by sending bad data. Ensuring the integrity of data is essential for a secure web application.
Preventing Injection Attacks
Injection attacks are a common threat. Attackers can manipulate your application by sending harmful data. Here are some strategies to prevent these attacks:
- Use Prepared Statements: They separate data from commands.
- Employ ORM Tools: Object-Relational Mapping tools can help.
- Limit User Input: Restrict the type and length of input.
- Escape User Input: Convert special characters to safe formats.
By implementing these measures, you can significantly reduce the risk of injection attacks.
Validating User Inputs
Validating user inputs is essential for maintaining application security. It ensures that only valid data enters your system. Here are some effective validation techniques:
- Whitelist Validation: Allow only specific, safe characters.
- Type Checking: Ensure data matches expected types.
- Range Checking: Verify that numeric inputs fall within acceptable limits.
- Format Checking: Use regular expressions to validate formats.
Implementing these validation techniques helps maintain data integrity.
Keep your application safe by regularly updating your validation rules. Monitor for new vulnerabilities and adjust as needed.

Credit: www.fastly.com
Rate Limiting And Throttling
Securing API endpoints is crucial for modern web applications. Rate limiting and throttling help manage user requests. They protect APIs from abuse and ensure fair usage. Let’s explore their benefits and how to set them up correctly.
Benefits Of Rate Limiting
Rate limiting brings several advantages:
- Prevents Abuse: It stops users from overwhelming the server.
- Enhances Security: Reduces the risk of DDoS attacks.
- Improves Performance: Keeps server response times fast.
- Encourages Fair Usage: Ensures all users have equal access.
Implementing rate limits can save resources. It leads to a better user experience.
Setting Up Throttling Correctly
Throttling controls the number of requests over time. Here’s how to set it up:
- Define Limits: Decide how many requests are allowed in a timeframe.
- Choose a Strategy: Use sliding window or token bucket methods.
- Implement Response Codes: Return 429 status code for too many requests.
- Monitor Usage: Track API usage patterns and adjust limits as needed.
Here’s a simple code example:
app.use((req, res, next) => {
const userRequests = getUserRequests(req.user);
if (userRequests > LIMIT) {
return res.status(429).send('Too many requests');
}
next();
});
Regularly review your throttling settings. Adjust limits based on user behavior.
Logging And Monitoring Api Activity
Logging and monitoring API activity is vital for security. It helps track access, detect anomalies, and ensure data integrity. Proper logging practices can identify threats before they escalate.
Importance Of Detailed Logs
Detailed logs serve multiple purposes:
- Audit Trails: They provide a record of API usage.
- Error Tracking: Logs help identify issues quickly.
- Security Insights: They reveal unauthorized access attempts.
Each log entry should include:
| Log Detail | Description |
|---|---|
| Timestamp | Exact date and time of the request. |
| User ID | The identifier of the user making the request. |
| Endpoint Accessed | The specific API endpoint that was requested. |
| Response Code | Status of the API response. |
| IP Address | The origin of the request. |
Real-time Monitoring Solutions
Real-time monitoring enhances security. It allows instant detection of unusual activities. Various tools provide this capability:
- Log Management Tools: Collect and analyze log data.
- Intrusion Detection Systems (IDS): Alert on suspicious activities.
- API Gateways: Monitor and manage API traffic.
Consider these features for monitoring tools:
- Alerts: Immediate notifications for unusual access.
- Dashboards: Visual representation of API activity.
- Analytics: Insights into usage patterns.
Choose a solution that fits your needs. Regularly review logs and monitoring reports. This practice keeps your API secure.
Api Gateway Utilization
Securing API endpoints is crucial in modern web applications. An API gateway acts as a protective barrier. It controls how users access your APIs. Proper utilization enhances security, performance, and scalability.
Role Of Api Gateways
API gateways serve multiple roles in web applications:
- Traffic Management: They manage incoming traffic effectively.
- Authentication: Gateways handle user authentication securely.
- Rate Limiting: They limit requests to prevent abuse.
- Logging: Gateways log requests for monitoring and debugging.
- Routing: They direct traffic to the correct service.
These roles ensure that your APIs are not only secure but also efficient.
Choosing The Right Api Gateway
Selecting the best API gateway is vital. Consider these factors:
| Feature | Importance |
|---|---|
| Scalability | Handles growing traffic smoothly. |
| Security | Offers robust security features. |
| Ease of Use | Simplifies management and deployment. |
| Cost | Fits within your budget constraints. |
| Integration | Works well with existing infrastructure. |
Evaluate these features carefully. Make sure the gateway aligns with your application needs.
Continuous Security Testing And Updates
Securing API endpoints is crucial for modern web applications. Continuous security testing ensures vulnerabilities are identified and fixed promptly. Regular updates maintain the integrity and safety of your APIs. This process prevents unauthorized access and data breaches.
Automated Security Testing
Automated security testing simplifies the process of finding flaws. Tools scan APIs for vulnerabilities quickly and efficiently. Here are some benefits of automated testing:
- Speed: Tests run faster than manual methods.
- Consistency: Automated tests provide uniform results.
- Scalability: Easily test multiple APIs simultaneously.
Consider using these popular tools for automated security testing:
| Tool Name | Functionality |
|---|---|
| OWASP ZAP | Open-source web application scanner. |
| Postman | API testing and monitoring. |
| Burp Suite | Comprehensive web security testing. |
Keeping Apis Up-to-date
Regular updates to APIs enhance security. Outdated APIs can expose vulnerabilities. Follow these steps to ensure your APIs remain secure:
- Monitor: Track API usage and performance regularly.
- Patch: Apply security patches immediately.
- Review: Conduct regular code reviews for vulnerabilities.
- Document: Keep clear documentation of changes and updates.
Stay informed about the latest security threats. Join forums and subscribe to security newsletters. Implementing timely updates helps protect sensitive data.
Educating Developers And End-users
Securing API endpoints is vital for modern web applications. Educating both developers and end-users strengthens security. Awareness reduces risks. A well-informed team can prevent many threats. Focus on two key areas: Security Awareness Training and Creating a Security-First Culture.
Security Awareness Training
Security awareness training empowers developers and users. It teaches them to recognize threats and respond effectively. Here are key topics to cover:
- Phishing Attacks: Identify suspicious emails and links.
- Strong Passwords: Use complex passwords and change them regularly.
- Data Privacy: Understand the importance of protecting personal data.
- Secure Coding Practices: Follow best practices while coding APIs.
Implement training sessions regularly. Use interactive methods like:
- Workshops
- Online Courses
- Quizzes
| Training Method | Benefits |
|---|---|
| Workshops | Hands-on experience and real-time feedback. |
| Online Courses | Flexible learning at one’s own pace. |
| Quizzes | Assess knowledge retention and understanding. |
Creating A Security-first Culture
A security-first culture fosters awareness. It encourages everyone to prioritize security. Here are steps to create this culture:
- Leadership Involvement: Leaders should model security behaviors.
- Regular Communication: Share security updates and best practices.
- Recognition Programs: Reward employees for reporting security issues.
- Open Discussions: Allow team members to voice concerns about security.
Encourage collaboration between teams. Developers should work closely with security experts. This partnership enhances knowledge sharing. Create a feedback loop for continuous improvement.
Conclusion: Building A Secure Api Ecosystem
Securing API endpoints is vital for modern web applications. A strong security strategy protects data and builds trust. Implementing the right measures helps prevent unauthorized access.
Summarizing Key Takeaways
- Authentication is crucial. Use OAuth or JWT.
- Rate limiting prevents abuse. Control user requests effectively.
- Data validation ensures only safe data enters your system.
- Encryption secures data in transit. Always use HTTPS.
- Regular audits identify vulnerabilities. Check APIs frequently.
Future Of Api Security
The future of API security looks promising. Innovations will enhance protection. Expect to see:
- AI-driven security to predict attacks.
- More automation in monitoring and response.
- Enhanced privacy features for users.
- Stronger compliance with data protection laws.
Investing in API security today prepares for tomorrow’s challenges. Secure APIs will lead to safer web applications.
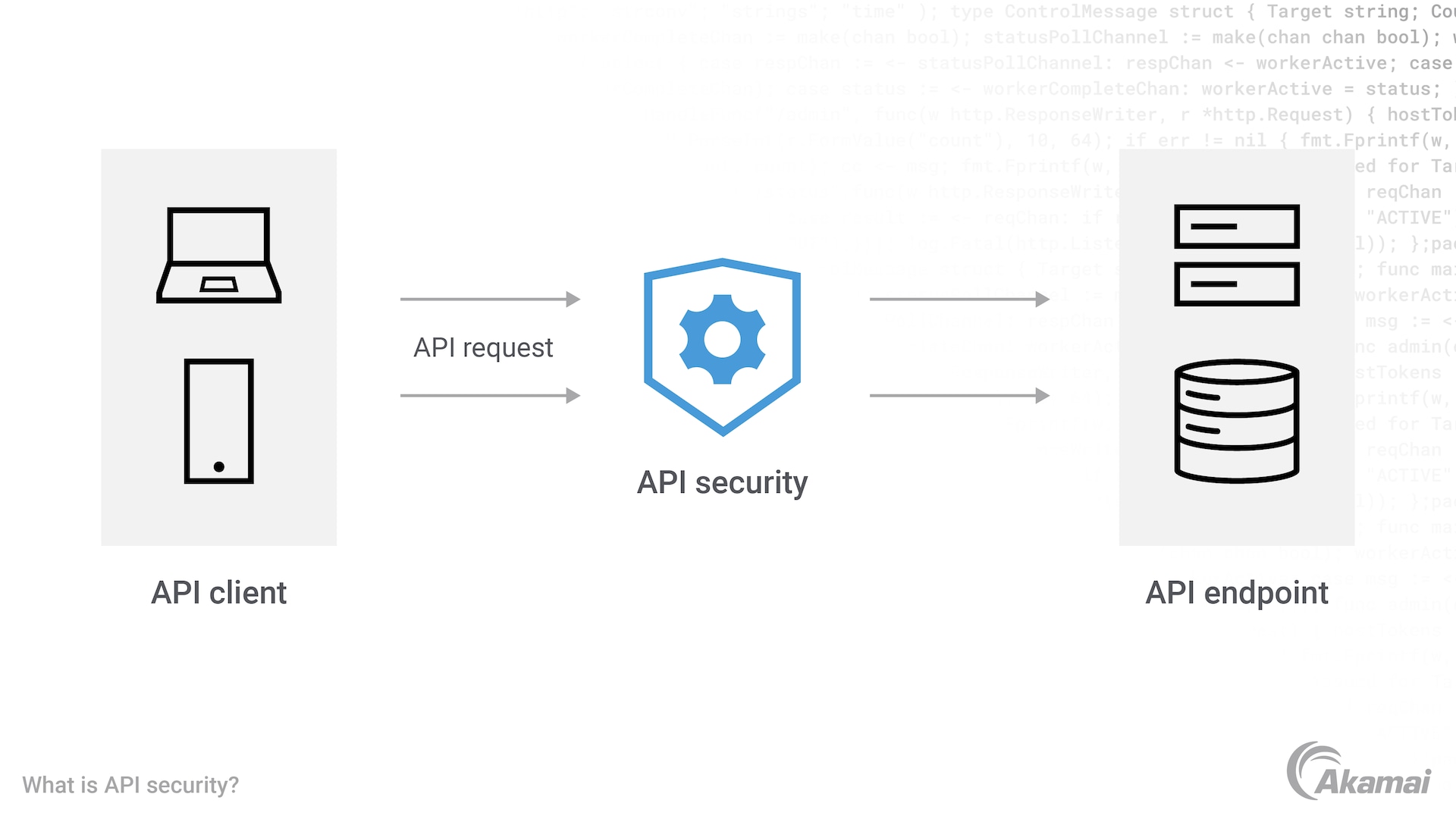
Credit: www.akamai.com
Frequently Asked Questions
How Can I Secure Api Endpoints Effectively?
Securing API endpoints involves multiple strategies. Use HTTPS to encrypt data in transit. Implement authentication methods like OAuth or API keys. Additionally, employ rate limiting to prevent abuse. Regularly audit and update your security measures to stay ahead of potential threats.
What Are Common Api Security Best Practices?
Common best practices include using HTTPS, validating inputs, and implementing authentication. Ensure proper access controls are in place. Regularly monitor logs for unusual activity. Keep your software up-to-date to protect against vulnerabilities. These practices help safeguard your API from attacks.
Why Is Api Authentication Important?
API authentication verifies user identity before granting access. It prevents unauthorized access to sensitive data. Without proper authentication, APIs are vulnerable to attacks. Strong authentication methods like OAuth enhance security by ensuring only legitimate users can interact with your API.
What Tools Can Help Secure Apis?
Several tools can enhance API security. API gateways like Kong or Apigee offer authentication and monitoring features. Security testing tools like OWASP ZAP can identify vulnerabilities. Additionally, using Web Application Firewalls (WAF) can help block malicious traffic. Choose tools that fit your specific needs.
Conclusion
Securing API endpoints is essential for protecting your web application. Implementing best practices, such as authentication and rate limiting, enhances security. Regularly testing your APIs for vulnerabilities is vital. By prioritizing these strategies, you can safeguard user data and maintain trust in your application.
Stay proactive and vigilant in your security efforts.




Leave a Reply