Application security compliance in healthcare ensures that sensitive patient data is protected according to regulatory standards. Key frameworks include HIPAA and HITECH, which mandate strict security measures.
Guide to Application Security Compliance for Healthcare:Healthcare organizations face increasing pressure to maintain application security compliance. As cyber threats grow, safeguarding patient information becomes paramount. Compliance not only protects sensitive data but also builds trust with patients. Understanding key regulations like HIPAA and HITECH is essential for any healthcare provider.
These frameworks outline requirements for data protection and breach notification. Organizations must adopt best practices in application security to mitigate risks. Regular audits, employee training, and robust encryption methods are crucial. Staying informed about evolving regulations can ensure ongoing compliance and enhance overall security strategies in the healthcare sector.
Introduction To Healthcare Application Security
Healthcare application security is crucial for protecting sensitive information. With the rise of digital health solutions, safeguarding patient data is more important than ever. Hackers target healthcare applications, making security a top priority for organizations.
The Importance Of Protecting Patient Data
Patient data includes personal and medical information. This information is valuable and can be misused. Protecting patient data has several key benefits:
- Trust: Patients expect their data to be safe.
- Compliance: Regulations require strict data protection.
- Reputation: Breaches can damage a healthcare organization’s reputation.
- Financial Security: Data breaches can lead to costly penalties.
Organizations must implement strong security measures to avoid breaches. Regular audits and updates are essential for maintaining security.
Regulatory Landscape For Healthcare Applications
The healthcare industry is highly regulated. Organizations must follow specific laws to protect patient data. Key regulations include:
| Regulation | Description |
|---|---|
| HIPAA | Protects sensitive patient information and sets standards for data privacy. |
| HITECH | Encourages the adoption of health information technology. |
| GDPR | Regulates data protection and privacy in the European Union. |
Compliance with these regulations is mandatory. Non-compliance can lead to severe penalties. Organizations must train employees about these laws.
Key Regulations In Healthcare Security
Healthcare security involves strict regulations. These rules protect patient data. Understanding these regulations is crucial for compliance.
Hipaa And Hitech Act Compliance
The Health Insurance Portability and Accountability Act (HIPAA) is vital for healthcare security. It sets standards for protecting patient information. All healthcare providers must follow these rules.
The HITECH Act expands HIPAA regulations. It encourages the use of electronic health records (EHRs). It also increases penalties for non-compliance.
| Regulation | Key Focus | Compliance Requirements |
|---|---|---|
| HIPAA | Protect patient privacy | Implement safeguards for data |
| HITECH | Encourage EHR use | Report breaches within 60 days |
- Train staff on data protection.
- Conduct regular risk assessments.
- Update policies as needed.
Gdpr Considerations For Global Healthcare Providers
The General Data Protection Regulation (GDPR) affects global healthcare providers. It focuses on data privacy for all EU citizens. Non-compliance can lead to heavy fines.
Key points of GDPR include:
- Obtain clear consent from patients.
- Allow patients to access their data.
- Report data breaches within 72 hours.
Healthcare providers must ensure:
- Data is stored securely.
- Patients understand their rights.
- Data processing is transparent.
Compliance with HIPAA and GDPR ensures trust. It protects both patients and providers.
Risk Assessment Strategies
Risk assessment strategies play a vital role in healthcare application security. They help identify weaknesses and prioritize actions to protect sensitive data. Effective risk assessments reduce potential threats and enhance compliance.
Identifying Vulnerabilities In Healthcare Applications
Identifying vulnerabilities is the first step in risk assessment. Healthcare applications often face unique challenges. Common vulnerabilities include:
- Weak authentication methods
- Insecure data storage
- Unpatched software
- Improper access controls
- Inadequate encryption
Conduct regular scans and audits. Use automated tools to detect security flaws. Engage security professionals to perform manual assessments. Collect data on known vulnerabilities from:
- National Vulnerability Database (NVD)
- OWASP Top Ten
- Security advisories
Regular updates to this data are crucial. This ensures the identification of new threats.
Prioritizing Risks For Remediation
Prioritizing risks helps allocate resources effectively. Start by evaluating the impact of each vulnerability. Consider the following factors:
| Factor | Description |
|---|---|
| Impact | Potential damage from a security breach. |
| Likelihood | Chance of a vulnerability being exploited. |
| Compliance | Regulatory requirements affecting the application. |
Use a risk matrix to visualize and prioritize vulnerabilities. Focus on high-impact, high-likelihood risks first.
Regularly review and update your risk assessment. This keeps your application security measures effective and compliant.

Credit: www.amazon.com
Building A Culture Of Security
Creating a strong culture of security is vital for healthcare organizations. Staff must understand the importance of protecting sensitive data. A proactive approach reduces risks and helps maintain patient trust. Establishing this culture starts with training and clear policies.
Training Staff On Security Best Practices
Effective training is essential for all employees. Regular sessions ensure that everyone is aware of security protocols. Here are key topics to include:
- Recognizing Phishing Attempts: Teach staff to spot suspicious emails.
- Strong Password Policies: Encourage using complex passwords and changing them regularly.
- Data Handling Procedures: Train staff on proper data storage and sharing methods.
- Incident Reporting: Ensure employees know how to report security issues quickly.
Interactive training methods can boost engagement. Use quizzes, role-playing, and real-life scenarios to reinforce learning. Consider setting up a security champions program. This empowers selected staff to promote security awareness among peers.
Developing Policies For Data Protection
Clear policies guide staff on data protection. These policies should be simple and easy to follow. Key elements to include are:
| Policy Area | Description |
|---|---|
| Access Control | Limit access to sensitive information based on job roles. |
| Data Encryption | Encrypt sensitive data during storage and transmission. |
| Device Security | Ensure all devices have up-to-date security software. |
| Regular Audits | Conduct audits to assess compliance with security policies. |
Make policies accessible to all staff. Regularly review and update them to reflect new threats. Ensure everyone understands their roles in protecting data. This shared responsibility strengthens the overall security posture.
Technical Safeguards For Applications
Technical safeguards play a crucial role in healthcare application security. They help protect sensitive patient data from unauthorized access. Organizations must implement these safeguards to comply with regulations. This section covers two key areas: encryption and access control mechanisms.
Encryption And Data Masking Techniques
Encryption secures data by converting it into a code. Only authorized users can decrypt and access the information. This process helps protect data in transit and at rest.
Data masking hides sensitive information. For example, a patient’s Social Security Number can be replaced with a placeholder. This allows users to work with data without exposing real information.
| Technique | Description | Benefits |
|---|---|---|
| Encryption | Transforms data into a secure format. | Protects data from unauthorized access. |
| Data Masking | Replaces sensitive data with non-sensitive data. | Allows safe data usage for testing. |
Implementing Access Control Mechanisms
Access control mechanisms limit who can view or use data. Effective controls protect sensitive information. They ensure that only authorized personnel can access applications.
- Role-Based Access Control (RBAC): Grants access based on user roles.
- Multi-Factor Authentication (MFA): Requires two or more verification methods.
- Audit Logs: Track user activity for security monitoring.
These mechanisms help prevent data breaches. Regularly review and update access controls. This keeps security measures effective against new threats.
Regular Security Audits And Monitoring
Regular security audits and monitoring are essential for healthcare compliance. They help organizations identify vulnerabilities and protect sensitive data. This process ensures patient information remains secure. It also builds trust with patients and stakeholders.
Conducting Comprehensive Security Audits
Comprehensive security audits evaluate the entire security posture of an organization. These audits assess policies, procedures, and technology. Here are key steps to conducting effective audits:
- Define Scope: Determine what systems and processes to audit.
- Gather Information: Collect data on current security practices.
- Identify Vulnerabilities: Look for weaknesses in systems and processes.
- Assess Risks: Evaluate the impact of identified vulnerabilities.
- Report Findings: Document results and provide recommendations.
Regular audits should occur at least annually. They can help maintain compliance with regulations like HIPAA.
Continuous Monitoring For Suspicious Activities
Continuous monitoring is vital for detecting suspicious activities in real-time. This process allows healthcare organizations to respond quickly to potential threats. Key components of continuous monitoring include:
| Component | Description |
|---|---|
| Intrusion Detection Systems (IDS) | Tools that monitor network traffic for suspicious activity. |
| Log Management | Collect and analyze logs for unusual patterns. |
| Access Control Monitoring | Track user access to sensitive data and systems. |
| Incident Response Plans | Prepare protocols for responding to detected threats. |
Establishing a routine for continuous monitoring is crucial. It helps organizations maintain a strong security posture. Regular updates and training keep staff aware of security practices.
Incident Response And Management
Incident Response and Management is crucial for healthcare security. It involves identifying, managing, and mitigating security incidents. A strong plan helps protect sensitive patient data. This section covers key components of incident response.
Developing An Effective Incident Response Plan
An effective incident response plan (IRP) ensures a swift reaction to security breaches. Here are essential steps to create one:
- Define Roles and Responsibilities: Assign specific tasks to team members.
- Establish Communication Protocols: Outline how to report incidents.
- Identify Critical Assets: List important data and systems.
- Create a Response Checklist: Develop a step-by-step guide for incidents.
- Regular Training: Conduct drills to prepare the team.
Ensure the plan is easily accessible. Update it regularly to reflect new threats. Involve all stakeholders in the process.
Post-incident Evaluation And Reporting
After an incident, evaluation and reporting are vital. This phase helps improve future responses. Follow these steps for effective evaluation:
- Gather Data: Collect logs and incident reports.
- Analyze the Incident: Determine what happened and how.
- Identify Weaknesses: Find gaps in your security measures.
- Prepare a Report: Document findings and recommendations.
Consider using a table to summarize key findings:
| Incident Type | Impact Level | Recommended Actions |
|---|---|---|
| Data Breach | High | Notify affected parties, enhance security measures |
| Malware Attack | Medium | Isolate affected systems, conduct malware removal |
| Phishing Attempt | Low | Train staff on identifying phishing emails |
Share the report with relevant teams. Use insights gained to improve the incident response plan. Continuous improvement is key to maintaining compliance.
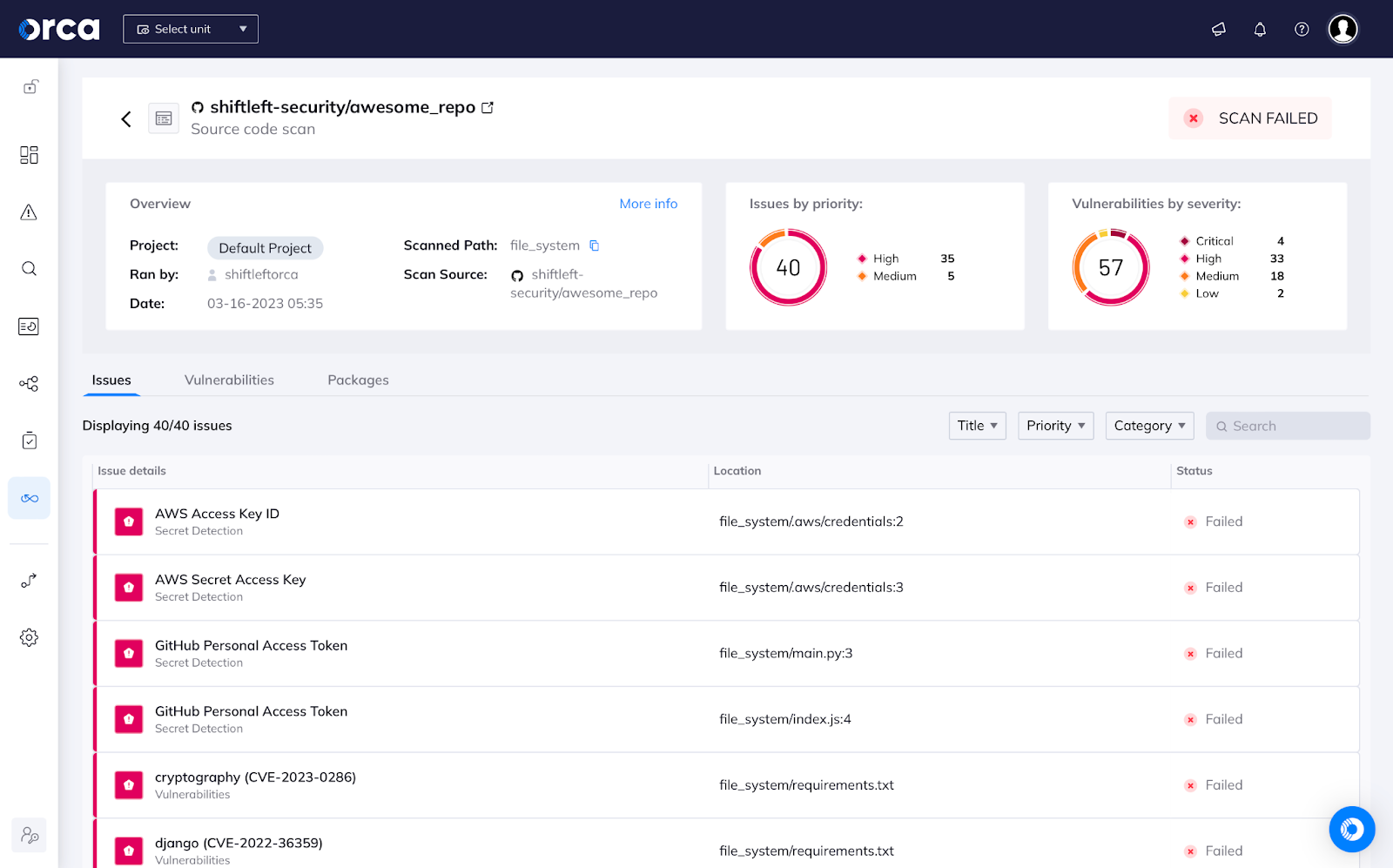
Credit: orca.security
Staying Current With Compliance Requirements
Healthcare organizations face constant changes in compliance regulations. Keeping up with these changes is crucial. Non-compliance can lead to severe penalties. Implementing effective strategies can ensure compliance.
Updating Security Measures With Evolving Regulations
Regulations like HIPAA and HITECH evolve regularly. Organizations must update their security measures promptly. Here are key steps to consider:
- Regular Audits: Conduct audits at least once a year.
- Employee Training: Train staff on new regulations and practices.
- Policy Review: Review and update policies every six months.
- Incident Response Plan: Ensure plans are current and effective.
Document all changes and updates. This practice builds accountability and transparency. Establish a dedicated compliance team to oversee these tasks.
Leveraging Technology For Compliance Management
Technology plays a vital role in managing compliance. Various tools can streamline the process. Consider the following technologies:
| Technology | Purpose |
|---|---|
| Compliance Management Software | Tracks changes and manages compliance documentation. |
| Data Encryption Tools | Protects sensitive patient data from breaches. |
| Audit Management Software | Facilitates regular audits and tracks findings. |
| Training Platforms | Educates staff on compliance and security measures. |
Use these technologies to simplify compliance management. Automating tasks reduces human error. Regularly review and update technology tools to ensure effectiveness.
Case Studies: Compliance In Action
Understanding application security compliance in healthcare is vital. Real-world examples reveal how organizations implement measures. These case studies illustrate both success and challenges faced.
Successful Implementation Of Compliance Measures
One notable case involves HealthTech Solutions. They adopted a multi-layered security approach. Their strategy included:
- Regular risk assessments
- Employee training programs
- Secure coding practices
- Data encryption
After implementing these measures, HealthTech Solutions saw a:
| Metric | Before Compliance | After Compliance |
|---|---|---|
| Data Breaches | 5 per year | 0 |
| Employee Awareness | 30% | 95% |
This case highlights how effective compliance measures reduce risks and enhance security.
Lessons Learned From Security Breaches
Another case to review is City Medical Center. They faced a significant data breach in 2021. Key lessons emerged from this incident:
- Prioritize employee training.
- Implement regular software updates.
- Conduct frequent security audits.
The breach resulted in:
- Compromised patient data
- Legal penalties
- Loss of patient trust
City Medical Center learned the hard way. They revamped their security protocols afterward. This case emphasizes the need for constant vigilance.
Credit: medium.com
Frequently Asked Questions
What Is Application Security Compliance In Healthcare?
Application security compliance in healthcare ensures that software applications meet regulatory standards. These standards protect patient data and maintain confidentiality. Compliance involves following guidelines such as HIPAA and ensuring that security measures are in place. This helps healthcare organizations mitigate risks and enhance patient trust.
Why Is Compliance Important For Healthcare Applications?
Compliance is crucial for healthcare applications to protect sensitive data. Non-compliance can lead to severe penalties and legal issues. It also safeguards patient privacy and fosters trust between healthcare providers and patients. Ultimately, compliance enhances the overall security posture of healthcare organizations.
What Are The Key Regulations For Healthcare Applications?
Key regulations for healthcare applications include HIPAA, HITECH, and GDPR. HIPAA sets standards for protecting patient health information. HITECH promotes the adoption of electronic health records. GDPR focuses on data protection for individuals in the European Union, impacting global healthcare practices.
How Can Healthcare Organizations Ensure Compliance?
Healthcare organizations can ensure compliance by conducting regular risk assessments. They should implement strong security measures and employee training programs. Regular audits and updates to security protocols are essential. Collaborating with compliance experts also helps maintain adherence to regulations.
Conclusion
Ensuring application security compliance in healthcare is vital for protecting sensitive patient data. Organizations must stay informed about regulations and best practices. Regular audits and employee training can enhance security measures. By prioritizing compliance, healthcare providers can build trust and safeguard their systems against potential threats.
Take action today for a secure future.




Leave a Reply