To implement application security in cloud environments, start by conducting a thorough risk assessment. Then, apply security best practices such as encryption, access controls, and regular vulnerability assessments.
How to Implement Application Security in Cloud Environments:Cloud environments offer flexibility and scalability but also introduce unique security challenges. As organizations increasingly migrate to the cloud, securing applications becomes essential. Application security involves protecting software from threats throughout its lifecycle. This includes secure coding practices, regular updates, and monitoring.
A robust security posture minimizes risks and ensures compliance with industry regulations. By adopting a proactive approach, businesses can safeguard sensitive data and maintain user trust. Understanding the shared responsibility model in cloud security is crucial, as it delineates the roles of both the cloud provider and the organization in maintaining security.
Introduction To Cloud Application Security
Cloud application security protects data and applications in cloud environments. Businesses store sensitive information online. This creates a need for strong security measures. Understanding cloud application security is crucial for all organizations.
The Importance Of Security In The Cloud
Security in the cloud is vital for several reasons:
- Data Protection: Safeguards sensitive information from breaches.
- Compliance: Meets legal and regulatory requirements.
- Trust: Builds customer confidence in your services.
- Business Continuity: Ensures operations continue during incidents.
Without proper security, organizations face serious risks. Data theft can lead to financial losses. Customers may lose trust in your brand. Effective security measures protect both assets and reputation.
Challenges Unique To Cloud Environments
Cloud environments present unique security challenges:
- Shared Responsibility: Security roles are divided between provider and user.
- Data Breaches: Increased risk of unauthorized access to data.
- Misconfiguration: Human errors can expose sensitive data.
- Compliance Complexity: Navigating various regulations can be tough.
| Challenge | Description |
|---|---|
| Shared Responsibility | Both provider and user must ensure security. |
| Data Breaches | Higher chances of attacks on cloud-stored data. |
| Misconfiguration | Errors in setup can lead to vulnerabilities. |
| Compliance Complexity | Different regulations complicate security measures. |
Organizations must address these challenges. This ensures a secure cloud environment for applications and data.
Foundational Security Principles
Implementing application security in cloud environments requires strong foundational principles. These principles guide organizations in protecting their data and applications effectively. Focus on the following key principles to enhance security:
Least Privilege Access
The principle of least privilege access limits user permissions. Each user should only have the access needed to perform their job. This reduces the risk of unauthorized actions.
- Identify user roles and responsibilities.
- Assign permissions based on necessity.
- Regularly review and update access rights.
Implementing this principle helps in:
- Minimizing potential damage from attacks.
- Enhancing accountability for user actions.
- Reducing the attack surface area.
Defense In Depth
Defense in depth employs multiple layers of security. This strategy protects against various threats. Should one layer fail, others remain to defend.
| Layer | Security Measure |
|---|---|
| Network | Firewalls and Intrusion Detection Systems (IDS) |
| Application | Web Application Firewalls (WAF) and Code Reviews |
| Data | Encryption and Backup Solutions |
Utilizing this principle enhances security through:
- Redundant protections against failures.
- Layered defense mechanisms.
- Continuous monitoring for threats.
Security By Design
Security by design means integrating security into the development process. Begin security planning from the start of projects. This approach reduces vulnerabilities in the final product.
- Incorporate security requirements in early stages.
- Perform threat modeling during development.
- Conduct regular security testing and assessments.
This principle fosters:
- More secure applications from the outset.
- Proactive identification of potential risks.
- Efficiency in addressing security flaws.
Designing A Secure Cloud Architecture
Creating a secure cloud architecture is crucial. It protects applications and data in cloud environments. A well-designed architecture reduces vulnerabilities. It also ensures compliance with security standards.
Choosing The Right Cloud Service Model
Selecting the right cloud service model is essential for security. There are three main models:
- Infrastructure as a Service (IaaS) – Offers basic computing resources.
- Platform as a Service (PaaS) – Provides a platform for developing apps.
- Software as a Service (SaaS) – Delivers software applications over the internet.
Each model has different security responsibilities:
| Service Model | Security Responsibility |
|---|---|
| IaaS | User manages OS, applications, and data. |
| PaaS | User manages applications and data only. |
| SaaS | Provider manages everything except user data. |
Choose the model that fits your security needs best.
Isolation Strategies For Multi-tenancy
Multi-tenancy allows multiple users to share resources. Use these strategies for effective isolation:
- Virtual Private Cloud (VPC) – Creates a private network within the cloud.
- Containerization – Uses containers to isolate applications.
- Network Segmentation – Divides the network into smaller, secure segments.
These strategies enhance security. They prevent unauthorized access to sensitive data.
Data Encryption Best Practices
Data encryption protects sensitive information in transit and at rest. Follow these best practices:
- Use Strong Encryption Algorithms – AES-256 is highly recommended.
- Encrypt Data at Rest – Protects data stored on cloud servers.
- Encrypt Data in Transit – Use TLS/SSL for secure data transfer.
- Regularly Update Encryption Keys – Prevents unauthorized access.
Implementing strong encryption practices enhances overall data security.

Credit: www.youtube.com
Identity And Access Management
Identity and Access Management (IAM) is crucial for cloud security. It ensures that only authorized users can access sensitive data and applications. Proper IAM helps prevent breaches and data loss.
Implementing Strong Authentication
Strong authentication verifies user identities effectively. Use these methods to enhance security:
- Multi-Factor Authentication (MFA): Requires two or more verification methods.
- Biometric Authentication: Uses fingerprints or facial recognition.
- Time-Based One-Time Passwords (TOTP): Generates unique codes every few seconds.
Strong authentication reduces the risk of unauthorized access. It adds an extra layer of security for user accounts.
Role-based Access Controls
Role-Based Access Control (RBAC) limits user access based on their role. This method helps manage permissions effectively. Follow these steps to implement RBAC:
- Define Roles: Identify the roles within your organization.
- Assign Permissions: Give permissions based on the role’s needs.
- Regularly Review Roles: Update roles and permissions as needed.
RBAC simplifies user management. It prevents users from accessing data they do not need.
Managing Security Credentials
Managing security credentials is vital for protecting cloud applications. Secure your credentials using these best practices:
| Practice | Description |
|---|---|
| Use Strong Passwords | Create complex passwords with letters, numbers, and symbols. |
| Rotate Credentials | Change passwords regularly to reduce risk. |
| Store Securely | Use a password manager for safe storage. |
| Limit Access | Share credentials only with necessary personnel. |
Proper management of security credentials prevents unauthorized access. It ensures that sensitive information remains protected.
Protecting Data In The Cloud
Data protection is vital for cloud environments. With sensitive information stored online, securing this data is essential. Implementing strong measures helps prevent unauthorized access and data loss.
Data Encryption And Tokenization
Data encryption protects information by turning it into unreadable code. Only authorized users can decode this information. Here are the key points:
- Use strong encryption algorithms like AES-256.
- Encrypt data both at rest and in transit.
- Tokenization replaces sensitive data with unique identifiers.
Tokenization helps minimize the risk of data breaches. It makes stolen data useless. Implementing both encryption and tokenization enhances data security significantly.
Backup And Recovery Solutions
Backing up data is crucial for recovery. Backup solutions store copies of data safely. They ensure quick restoration after a loss. Consider these options:
- Use automated backup tools to schedule regular backups.
- Store backups in multiple locations for added security.
- Test recovery processes frequently to ensure effectiveness.
Regular backups protect against data loss from attacks or disasters. Ensure that recovery plans are documented and easily accessible.
Handling Data Breaches
Despite best efforts, breaches can occur. Handling data breaches quickly is crucial. Follow these steps:
- Identify the breach source immediately.
- Contain the breach to limit damage.
- Notify affected parties without delay.
- Implement measures to prevent future breaches.
Having a clear response plan helps manage breaches effectively. Training staff on response procedures is essential. This ensures everyone knows their role during an incident.
Application Security Testing
Application Security Testing is crucial in cloud environments. It helps identify and fix vulnerabilities. This process ensures your applications are safe from attacks. Regular testing keeps your data secure and builds user trust.
Automated Vulnerability Scanning
Automated vulnerability scanning quickly finds security weaknesses. This tool scans your application and reports issues. It saves time and reduces human error.
- Schedule scans regularly.
- Integrate scans into the CI/CD pipeline.
- Review reports and prioritize fixes.
Many tools are available for scanning:
| Tool Name | Key Features |
|---|---|
| OWASP ZAP | Open-source, user-friendly, extensive community support. |
| Nessus | Comprehensive, customizable, extensive vulnerability database. |
| Burp Suite | Advanced features, manual testing tools, customizable plugins. |
Penetration Testing Methodologies
Penetration testing simulates real-world attacks. This method identifies weaknesses in your application. Different methodologies exist for effective testing.
- Black Box Testing: Testers have no prior knowledge.
- White Box Testing: Testers have full knowledge of the system.
- Gray Box Testing: Testers have partial knowledge.
Choose a methodology that fits your needs. Regular penetration testing improves security posture.
Code Review And Security Auditing
Code review and security auditing ensure secure coding practices. This process involves checking code for vulnerabilities.
- Use automated tools for code analysis.
- Conduct manual reviews for critical areas.
- Involve multiple team members for diverse perspectives.
Key aspects to focus on during reviews:
- Input validation
- Error handling
- Authentication and session management
Regular audits keep your application secure. They help prevent future vulnerabilities.
Monitoring And Incident Response
Effective monitoring and incident response are essential for cloud application security. They help identify and address threats quickly. Implementing these strategies can protect sensitive data and maintain business continuity.
Real-time Threat Detection
Real-time threat detection is crucial in cloud environments. It allows teams to spot issues as they happen. Here are some key components:
- Continuous Monitoring: Use tools to watch your applications 24/7.
- Behavioral Analysis: Track user behavior to find anomalies.
- Threat Intelligence: Leverage data from various sources to identify risks.
Consider using these technologies for enhanced detection:
| Technology | Description |
|---|---|
| SIEM Tools | Aggregate and analyze security data in real-time. |
| Intrusion Detection Systems | Monitor network traffic for suspicious activities. |
| Machine Learning | Automate detection of unusual patterns. |
Automated Response Mechanisms
Automated response mechanisms speed up incident handling. They reduce human error and allow for faster recovery. Key benefits include:
- Immediate Action: Automatically block malicious activities.
- Alerts: Send notifications to security teams.
- Playbooks: Use predefined procedures for common incidents.
Implementing automation tools can enhance your response:
- Choose a robust Security Orchestration tool.
- Integrate with existing security systems.
- Regularly update automation scripts.
Forensic Analysis In Cloud
Forensic analysis helps understand security incidents. It provides insights into how breaches occurred. Consider these steps for effective analysis:
- Data Collection: Gather logs and relevant data from cloud services.
- Evidence Preservation: Ensure data integrity during analysis.
- Incident Documentation: Keep detailed records of findings.
Utilize these tools for forensic analysis:
| Tool | Purpose |
|---|---|
| CloudTrail | Track user activity and API usage. |
| ELK Stack | Analyze log data for patterns. |
| Forensic Software | Recover deleted or hidden files. |
Implementing robust monitoring and incident response ensures your cloud environment remains secure. It protects your applications from evolving threats.
Compliance And Legal Considerations
Compliance and legal considerations are vital in cloud security. Organizations must follow laws and regulations. This ensures data protection and builds trust with users.
Adhering To Regulatory Standards
Regulatory standards vary by industry and region. Organizations must know applicable regulations. Common standards include:
- GDPR – Protects personal data in the EU.
- HIPAA – Governs health information in the U.S.
- PCI DSS – Secures credit card transactions.
Each standard has specific requirements. Organizations should:
- Identify applicable regulations.
- Implement necessary security measures.
- Train employees on compliance.
Data Sovereignty And Privacy Laws
Data sovereignty refers to data being subject to local laws. This impacts where data can be stored. Organizations must consider:
| Region | Law | Key Requirement |
|---|---|---|
| EU | GDPR | Data must stay within the EU. |
| U.S. | CCPA | Consumers have rights over personal data. |
| Australia | Privacy Act | Data must be protected and managed. |
Understanding local laws helps avoid legal issues. Ensure data storage complies with these laws.
Conducting Compliance Audits
Regular compliance audits are essential. They help identify gaps in security. Follow these steps for effective audits:
- Schedule audits regularly.
- Review compliance with regulations.
- Document findings and actions.
- Update security measures as needed.
Engaging a third-party auditor can provide an unbiased view. This strengthens the overall security posture.
Continuous Improvement And Education
Continuous improvement and education are essential for effective application security in cloud environments. Organizations must adapt to changing threats and technologies. A proactive approach ensures robust security measures are always in place.
Staying Updated With Cloud Security Trends
Cloud security trends evolve rapidly. Staying updated is crucial for effective defense strategies. Follow these steps:
- Subscribe to industry newsletters.
- Attend security conferences and webinars.
- Read whitepapers and research articles.
Key areas to monitor include:
| Trend | Description |
|---|---|
| Zero Trust Architecture | Assumes no user or device is trusted by default. |
| Automated Security Tools | Utilizes AI to detect and respond to threats. |
| Compliance Regulations | New laws impact security standards and practices. |
Training And Awareness Programs
Training ensures team members understand security best practices. Regular awareness programs boost the security culture. Implement these strategies:
- Conduct quarterly security training sessions.
- Use interactive quizzes to reinforce learning.
- Provide resources for self-paced learning.
Topics to cover include:
- Data protection techniques.
- Recognizing phishing attempts.
- Incident response procedures.
Feedback Loops And Security Policies Update
Feedback loops are vital for refining security measures. Regularly review and update security policies based on feedback. Consider these actions:
- Conduct security audits to identify gaps.
- Gather input from team members on security practices.
- Update policies to reflect new threats and technologies.
Establish a timeline for policy reviews:
| Review Frequency | Action |
|---|---|
| Monthly | Conduct internal audits. |
| Quarterly | Update training materials. |
| Annually | Review overall security policies. |
Implementing continuous improvement and education enhances application security in cloud environments.
Credit: cioinfluence.com
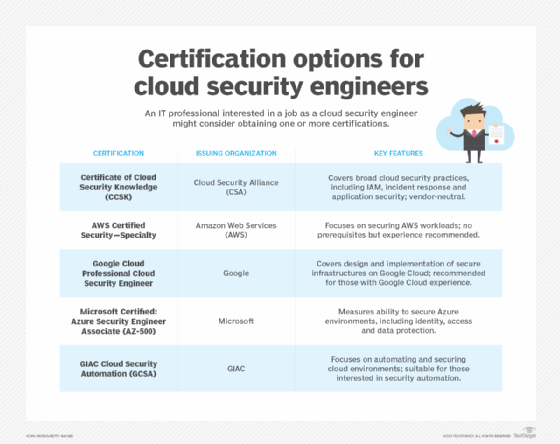
Credit: www.techtarget.com
Frequently Asked Questions
What Is Application Security In Cloud Environments?
Application security in cloud environments refers to measures taken to protect applications from threats. This includes implementing security protocols, conducting regular audits, and utilizing encryption. Organizations must also ensure compliance with industry standards and best practices. Effective application security reduces vulnerabilities and enhances overall cloud safety.
Why Is Application Security Important In The Cloud?
Application security is crucial in the cloud due to the shared responsibility model. It helps protect sensitive data from breaches and unauthorized access. As more businesses migrate to the cloud, the risk of cyberattacks increases. Strong application security measures safeguard business integrity and maintain customer trust.
How Can I Enhance Cloud Application Security?
You can enhance cloud application security by adopting several best practices. Start with regular security assessments and vulnerability testing. Implement multi-factor authentication and use encryption for data at rest and in transit. Training staff on security awareness also plays a vital role in mitigating risks.
What Are Common Cloud Application Security Risks?
Common cloud application security risks include data breaches, insecure APIs, and misconfigurations. Additionally, insider threats and account hijacking pose significant challenges. Understanding these risks helps organizations develop effective strategies to counteract them. Regular monitoring and updates are essential for maintaining cloud security.
Conclusion
Securing applications in cloud environments is crucial for protecting sensitive data. By implementing best practices like regular security assessments and robust access controls, organizations can mitigate risks effectively. Continuous monitoring and employee training also play vital roles. Prioritize application security to safeguard your cloud infrastructure and maintain customer trust.




Leave a Reply