Choosing the right cybersecurity solution involves assessing your company’s specific needs and evaluating available options. Focus on scalability, ease of use, and compliance with industry regulations.
Guide to Choosing a Cybersecurity Solution for Your Company:Cybersecurity is essential for protecting your company’s sensitive data and maintaining trust with customers. With increasing cyber threats, selecting an effective solution becomes crucial. Organizations face unique challenges that require tailored strategies. Start by identifying vulnerabilities within your current systems.
Consider the size of your business, the nature of your operations, and regulatory requirements. Research various solutions, including firewalls, antivirus software, and intrusion detection systems. A comprehensive approach not only mitigates risks but also enhances your overall security posture. Investing in the right cybersecurity measures safeguards your assets and promotes business continuity in an ever-evolving digital landscape.
Introduction To Cybersecurity In Business
Cybersecurity is vital for modern businesses. It protects data and systems from threats. Every company faces risks in the digital world. Understanding these risks helps in choosing the right solutions.
The Importance Of Digital Security
Digital security is crucial for several reasons:
- Data Protection: Safeguards sensitive information.
- Reputation Management: Maintains trust with clients.
- Regulatory Compliance: Meets legal requirements.
- Operational Continuity: Prevents business disruptions.
Investing in cybersecurity builds a strong foundation. It shows clients that you care about their data.
Risks Of Inadequate Cyber Protections
Not having strong cybersecurity can lead to severe issues:
- Data Breaches: Loss of sensitive information.
- Financial Loss: Costs for recovery can be high.
- Legal Consequences: Fines for not meeting regulations.
- Loss of Customer Trust: Clients may leave if their data is unsafe.
Companies must recognize these risks. A proactive approach can save time and money.
| Risk | Impact |
|---|---|
| Data Breach | Loss of customer data and privacy |
| Financial Loss | High costs for recovery and penalties |
| Legal Consequences | Fines and lawsuits |
| Loss of Customer Trust | Reduced sales and reputation damage |
Understanding these risks helps guide decision-making. Strong cybersecurity is not just an option; it’s essential.
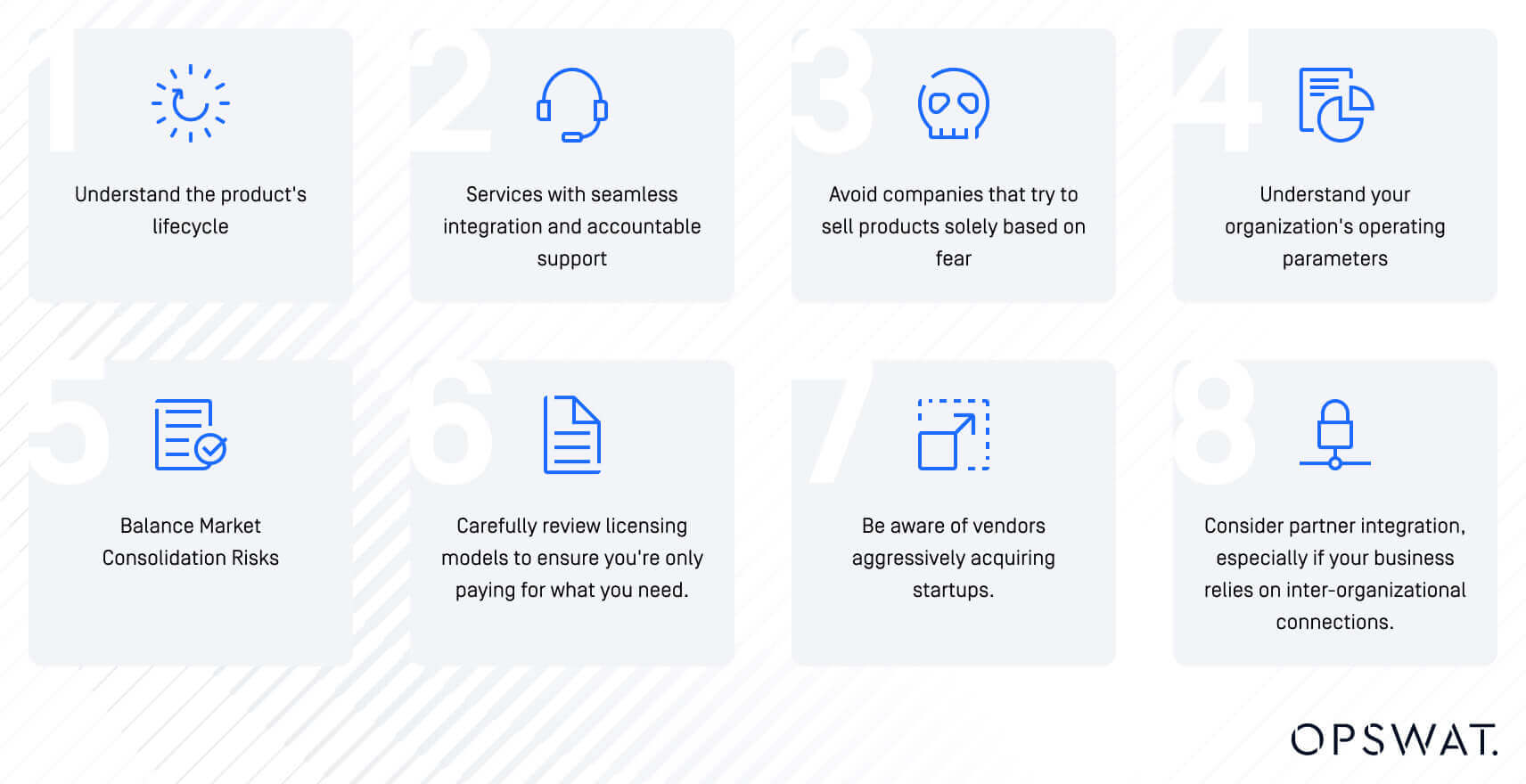
Credit: www.opswat.com
Evaluating Company Needs
Understanding your company’s unique requirements is crucial in choosing the right cybersecurity solution. Every business has distinct vulnerabilities and strengths. Evaluating needs helps you select the best protection available.
Assessing Your Digital Footprint
Your digital footprint includes all online activities. This covers websites, social media, and cloud services. Assessing it helps identify potential vulnerabilities.
- List all online platforms your company uses.
- Identify sensitive data stored on these platforms.
- Check for user access levels and permissions.
To better understand your digital presence, consider creating a table:
| Platform | Type of Data | Access Level |
|---|---|---|
| Website | Customer Data | Admin, User |
| Social Media | Marketing Data | Public, Admin |
| Cloud Services | Business Documents | Admin, Limited User |
Understanding Threat Landscape
- Phishing Attacks: Fraudulent emails trick users.
- Malware: Malicious software disrupts systems.
- Ransomware: Attackers hold data hostage for money.
- Data Breaches: Unauthorized access to sensitive information.
Stay updated on the latest threats by following cybersecurity news. This knowledge will help you make informed decisions.
“`
Types Of Cybersecurity Solutions
Choosing the right cybersecurity solution is vital for your company. Different solutions focus on various aspects of security. Here are some of the main types you should consider.
Firewalls And Network Security
Firewalls act as barriers between your network and threats. They monitor incoming and outgoing traffic.
- Types of firewalls include:
- Packet-filtering firewalls
- Stateful inspection firewalls
- Next-generation firewalls
Network security involves protecting your network from intrusions. Key elements include:
| Element | Description |
|---|---|
| Access Control | Limits who can enter your network. |
| VPN | Creates a secure connection over the internet. |
| Network Segmentation | Divides the network to enhance security. |
Endpoint Protection Platforms
Endpoint protection platforms (EPP) secure endpoints like computers and mobile devices. They prevent malware and unauthorized access.
- Key features of EPP include:
- Antivirus and anti-malware protection
- Data encryption
- Device control
Many EPP solutions offer:
- Real-time monitoring
- Threat intelligence
- Automated response capabilities
Intrusion Detection Systems
Intrusion Detection Systems (IDS) monitor your network for suspicious activity. They alert you to potential threats.
- Two main types of IDS are:
- Network-based IDS
- Host-based IDS
Key functions of IDS include:
| Function | Description |
|---|---|
| Traffic Analysis | Scans network traffic for anomalies. |
| Alerting | Notifies administrators of potential breaches. |
| Reporting | Provides detailed logs for analysis. |

Credit: www.beyondkey.com
Key Features To Consider
Selecting a cybersecurity solution requires careful thought. Focus on key features that ensure your company’s safety. These features can protect your business from various threats.
Real-time Monitoring Capabilities
Real-time monitoring is crucial for detecting threats quickly. Look for solutions that offer:
- 24/7 Monitoring: Continuous oversight of your network.
- Alert Systems: Immediate notifications for suspicious activities.
- Dashboard Access: User-friendly interface to view security status.
These capabilities help you respond swiftly to potential breaches. They also reduce the risk of significant damage.
Automated Response And Mitigation
Automated responses save time during an attack. Choose solutions that include:
- Instant Threat Isolation: Automatically cuts off infected devices.
- Predefined Actions: Specific steps taken during attacks.
- Regular Updates: Keeps defenses current against new threats.
Automation enhances efficiency. It allows your team to focus on other tasks.
Scalability And Integration
Your cybersecurity needs may grow. Ensure the solution can adapt by checking:
| Feature | Importance |
|---|---|
| Scalability: Easily add new users or features. | Supports business growth without major changes. |
| Integration: Works with existing systems. | Reduces costs and training time. |
Choosing scalable and integrative solutions ensures long-term success. It simplifies future upgrades and adjustments.
Budget Considerations
Choosing the right cybersecurity solution requires careful budgeting. Understanding costs helps in making informed decisions. Focus on maximizing security while managing expenses. Here are key aspects to consider.
Cost-benefit Analysis
Performing a cost-benefit analysis is essential. This analysis compares the costs of a cybersecurity solution with its benefits. Consider these points:
- Identify potential risks your company faces.
- Estimate the financial impact of a data breach.
- Calculate costs of implementing the solution.
- Assess potential savings from preventing breaches.
Use a simple table to visualize your findings:
| Item | Cost | Benefit |
|---|---|---|
| Data Breach Risk | $50,000 | Loss Avoidance |
| Cybersecurity Solution | $15,000 | Protection Against Breaches |
| Training Employees | $5,000 | Increased Awareness |
This table shows the clear benefits of investing in cybersecurity. A small investment can save your company from significant losses.
Understanding Total Cost Of Ownership
Calculating the total cost of ownership (TCO) is vital. TCO includes all costs associated with a cybersecurity solution. Consider these factors:
- Initial Costs: Purchase and installation expenses.
- Ongoing Costs: Maintenance and subscription fees.
- Training Costs: Employee training and awareness programs.
- Upgrade Costs: Future upgrades and enhancements.
Understanding TCO helps you budget effectively. It reveals the true cost of a solution over time. Make decisions based on complete financial insights.
Vendor Selection Criteria
Choosing the right cybersecurity solution is vital for your company. The vendor’s reputation, reliability, and support services play a significant role. Assessing these factors can help you make an informed choice.
Reputation And Reliability
Evaluate a vendor’s reputation in the cybersecurity industry. A strong reputation often indicates reliability. Consider the following points:
- Years in business
- Industry certifications
- Client reviews and testimonials
- Case studies showcasing successful implementations
Here’s a simple table to assess vendor reputation:
| Vendor | Years in Business | Certifications | Client Satisfaction |
|---|---|---|---|
| Vendor A | 10 | ISO 27001, PCI DSS | 95% |
| Vendor B | 5 | ISO 27001 | 88% |
| Vendor C | 15 | ISO 27001, SOC 2 | 90% |
Customer Support And Service Levels
Effective customer support is essential for cybersecurity solutions. Evaluate the service levels offered by vendors. Key aspects to consider include:
- Availability of support (24/7 vs. business hours)
- Response times for critical issues
- Modes of communication (phone, email, chat)
- Training and resources provided
Assess customer support through these questions:
- What is the average response time?
- Are they available on weekends and holidays?
- Do they offer self-service resources?
Choosing a vendor with strong support can enhance your cybersecurity posture.
Implementing Your Cybersecurity Solution
Implementing a cybersecurity solution requires careful planning. The right approach ensures safety and efficiency. Focus on deployment strategies and training programs. These elements create a robust defense against cyber threats.
Deployment Strategies
Choose a deployment strategy that fits your company’s needs. Here are common strategies:
- On-Premises: Install software on local servers.
- Cloud-Based: Use services hosted in the cloud.
- Hybrid: Combine on-premises and cloud solutions.
Each strategy has its own advantages:
| Strategy | Advantages |
|---|---|
| On-Premises | Full control and customization. |
| Cloud-Based | Scalability and lower costs. |
| Hybrid | Flexibility and balance of resources. |
Evaluate your company size and budget. Choose the strategy that meets your needs.
Training And Awareness Programs
Training is essential for effective cybersecurity. Employees must understand their role in security. Implement regular training sessions.
Focus on these key topics:
- Identifying phishing scams.
- Creating strong passwords.
- Reporting suspicious activities.
Utilize engaging methods for training:
- Interactive workshops.
- Online courses.
- Simulated phishing attacks.
Regularly refresh training content. Keep staff updated on new threats. Encourage a culture of security awareness.

Credit: contentmx.com
Regular Review And Update Procedures
Regular reviews and updates are essential for any cybersecurity solution. They help ensure your systems remain secure against new threats. Cybersecurity is an ongoing process. It needs constant attention and adjustment.
Scheduling Security Audits
Security audits are vital to identify vulnerabilities. Schedule them regularly to keep your systems safe. Consider the following audit frequency:
| Audit Type | Frequency |
|---|---|
| Internal Audits | Quarterly |
| External Audits | Annually |
| Compliance Audits | As Required |
Use these audits to assess:
- Network security
- Data protection
- User access controls
Make sure to document findings and action items. This will help track improvements over time.
Adapting To Emerging Threats
Cyber threats evolve constantly. Stay informed about new risks and trends. Use these strategies to adapt:
- Monitor industry news and updates.
- Participate in cybersecurity forums and groups.
- Implement threat intelligence tools.
Be proactive. Update your cybersecurity measures based on current threats. Regularly train staff on new risks. Awareness is key to prevention.
Legal And Compliance Issues
Choosing the right cybersecurity solution involves understanding legal and compliance issues. Companies face various laws that protect data. Not following these laws can lead to heavy fines. A solid cybersecurity plan helps you stay compliant.
Navigating Data Protection Laws
Data protection laws are crucial for all businesses. They define how to collect and store personal data. Here are some key laws:
- GDPR: Applies to companies dealing with EU citizens.
- CCPA: Focuses on consumer rights in California.
- PIPEDA: Governs data in Canada.
Each law has specific requirements. Your cybersecurity solution must address these needs.
Industry-specific Security Regulations
Different industries have unique security regulations. Compliance depends on your sector. Here are some examples:
| Industry | Regulation |
|---|---|
| Healthcare | HIPAA |
| Finance | GLBA |
| Education | FERPA |
These regulations require specific cybersecurity measures. Make sure your solution meets these standards.
Final Thoughts
Choosing a cybersecurity solution is crucial for your business. It protects your data and builds trust with customers. A strong cybersecurity strategy creates a safe environment for everyone.
Building A Culture Of Cybersecurity
Creating a culture of cybersecurity starts with awareness. Every employee plays a role in protecting company data. Here are key steps to develop this culture:
- Training: Provide regular training sessions on cybersecurity.
- Communication: Share updates on potential threats and best practices.
- Involvement: Encourage employees to report suspicious activities.
- Policy: Establish clear security policies and procedures.
- Leadership: Leaders should model good cybersecurity behavior.
Engagement is vital. Employees should feel responsible for protecting information. An informed team is your first line of defense.
Long-term Benefits Of A Robust Cybersecurity Strategy
Investing in a strong cybersecurity strategy yields many benefits:
| Benefit | Description |
|---|---|
| Data Protection | Safeguards sensitive company and customer information. |
| Reputation | Builds trust with clients through reliable security measures. |
| Regulatory Compliance | Aids in meeting legal and regulatory requirements. |
| Cost Savings | Reduces costs associated with data breaches and recovery. |
A robust cybersecurity strategy ensures long-term success. It protects your business from evolving threats. Invest wisely and stay ahead of potential risks.
Frequently Asked Questions
What Should I Consider When Choosing Cybersecurity Solutions?
When selecting a cybersecurity solution, consider your business size, industry, and specific needs. Assess the types of threats relevant to your organization. Evaluate compliance requirements and budget constraints. Finally, ensure the solution offers scalability and support for future growth.
How Do I Evaluate Cybersecurity Vendors?
To evaluate cybersecurity vendors, check their reputation, experience, and customer reviews. Look for certifications and industry recognition. Request demonstrations and trial periods to assess usability. Additionally, compare pricing, features, and customer support to find the best fit for your company.
Why Is Employee Training Important In Cybersecurity?
Employee training is crucial in cybersecurity because human error is a leading cause of breaches. Training raises awareness about threats like phishing and social engineering. It equips employees with the skills to recognize and respond to potential attacks. A well-informed workforce strengthens your overall security posture.
What Are The Common Types Of Cybersecurity Threats?
Common types of cybersecurity threats include malware, phishing, ransomware, and insider threats. Each type targets different vulnerabilities within an organization. Understanding these threats helps in implementing appropriate protective measures. Regular updates and employee training can mitigate these risks effectively.
Conclusion
Choosing the right cybersecurity solution is crucial for your company’s safety. Assess your specific needs and budget carefully. Prioritize solutions that offer comprehensive protection and reliable support. Engaging with experienced providers can make a significant difference. With the right approach, you can safeguard your digital assets and ensure business continuity.




Leave a Reply