To perform a vulnerability assessment ethically, obtain proper authorization and follow a structured methodology. Ensure all findings are reported responsibly.
How to Perform a Vulnerability Assessment Ethically:Vulnerability assessments are crucial for identifying security weaknesses in systems. Conducting these assessments ethically helps maintain trust and legal compliance. Start by securing explicit permission from the organization you are assessing. Without this, your actions could be considered illegal and unethical.
Use a structured approach, such as OWASP or NIST guidelines, to ensure thoroughness and consistency. Document all findings meticulously and report them to the relevant stakeholders. This responsible disclosure allows organizations to address vulnerabilities promptly, safeguarding their assets and data. Always respect confidentiality and privacy during the process to uphold professional integrity.

Credit: www.eccouncil.org
Introduction To Ethical Vulnerability Assessment
In today’s digital age, protecting systems from security threats is crucial. Ethical vulnerability assessment is a key part of this protection. It helps identify and fix security weaknesses.
Importance Of Ethics
Ethics guide how we conduct vulnerability assessments. Acting ethically ensures trust and integrity. Unethical behavior can harm systems and users. Ethical practices protect data and maintain privacy.
Consider these ethical guidelines:
- Always get permission before starting assessments.
- Respect user privacy and data confidentiality.
- Report findings honestly and accurately.
Key Objectives
Vulnerability assessments aim to find and fix security issues. They also help improve the overall security posture of systems.
Key objectives include:
- Identify vulnerabilities: Find weaknesses in the system.
- Assess risk: Determine the potential impact of vulnerabilities.
- Recommend fixes: Suggest ways to fix identified issues.
To summarize the key points:
| Ethics | Objectives |
|---|---|
| Get permission | Identify vulnerabilities |
| Respect privacy | Assess risk |
| Report honestly | Recommend fixes |
Preparing For The Assessment
Before starting a vulnerability assessment, preparation is crucial. Ethical assessments require a clear plan. This ensures efficiency and adherence to ethical guidelines. Proper preparation helps in identifying potential risks accurately.
Defining Scope
Start by defining the scope of the assessment. Identify which systems and networks need testing. Create a list of assets, including hardware and software. Determine the boundaries to avoid unauthorized access.
| Asset Type | Description | In Scope? |
|---|---|---|
| Servers | Web and database servers | Yes |
| Network Devices | Routers and switches | No |
| Applications | Customer-facing web apps | Yes |
Communicate with stakeholders to confirm the scope. Document all agreements to prevent misunderstandings. Make sure everyone knows what is included and excluded.
Gathering Necessary Tools
Gathering the right tools is essential for an effective assessment. Use both automated tools and manual techniques. Automated tools help in scanning for known vulnerabilities quickly.
- Vulnerability Scanners
- Network Analyzers
- Penetration Testing Tools
Manual techniques involve expert analysis. They help in identifying complex vulnerabilities. Ensure you have the latest versions of all tools. This ensures accurate results and up-to-date threat detection.
Create a checklist of all tools needed. Verify they are installed and configured correctly. This preparation step ensures a smooth assessment process.
Legal And Regulatory Considerations
Understanding the legal and regulatory considerations is essential for performing a vulnerability assessment ethically. This ensures you stay compliant with laws and avoid legal issues. Failing to adhere to these can result in severe penalties. Below are the key areas you need to focus on.
Compliance Requirements
Compliance is crucial in vulnerability assessments. Different sectors have specific compliance requirements that you must follow. These regulations ensure data protection and security. Here are a few common frameworks:
- GDPR – Protects personal data in the EU.
- HIPAA – Focuses on healthcare information in the USA.
- PCI DSS – Secures payment card data globally.
Understand the regulations that apply to your sector. This will help you conduct assessments within legal boundaries. Always stay updated on new rules and changes.
Permission And Authorization
Before starting a vulnerability assessment, obtain proper permission and authorization. Unauthorized scanning can be illegal and unethical. Follow these steps to ensure you have the necessary approvals:
- Identify the stakeholders involved.
- Get written consent from the organization.
- Ensure all parties understand the scope and objectives.
Document all permissions and keep records safe. This will protect you and the organization legally. Always respect the terms of the agreement.
Performing a vulnerability assessment ethically requires attention to legal and regulatory details. By following compliance requirements and obtaining proper permissions, you ensure a smooth and lawful assessment process.
Conducting Preliminary Research
Conducting preliminary research is a crucial step in performing an ethical vulnerability assessment. It helps you understand the landscape and prepares you for a thorough evaluation. This research sets the foundation for identifying and mitigating potential threats effectively.
Identifying Potential Threats
Start by identifying potential threats that could harm the system. Create a list of common vulnerabilities and threats. Use trusted sources like CVE databases, security forums, and industry reports.
- Common Vulnerabilities: SQL Injection, Cross-Site Scripting, Buffer Overflow.
- Threat Actors: Hackers, Insider Threats, Malicious Software.
Match these threats with the assets in your environment. This helps in understanding which systems are most at risk.
Understanding The Environment
Understanding the environment is key to a successful assessment. Gather information about the infrastructure and architecture.
| Component | Description |
|---|---|
| Network Topology | Layout of the network and its connections. |
| Operating Systems | Types and versions of OS in use. |
| Applications | Software and services running on the network. |
Document the tools and technologies used. Include firewalls, IDS/IPS, and encryption methods. This aids in pinpointing weak spots.
- List all hardware and software assets.
- Map out the network.
- Identify security controls in place.
Gathering this information helps in creating a comprehensive assessment plan. It ensures no stone is left unturned.
Executing The Assessment
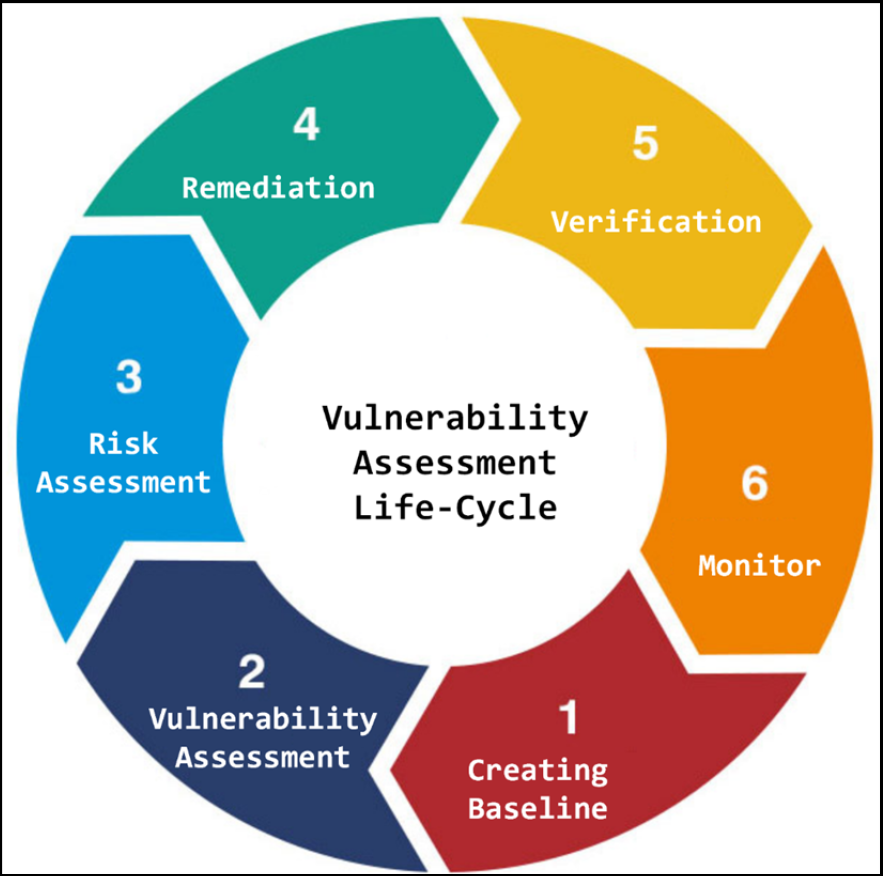
Executing a vulnerability assessment involves specific steps. Each step is crucial for finding and fixing security weaknesses. This section will guide you through the key phases of performing an ethical vulnerability assessment.
Scanning For Vulnerabilities
Scanning for vulnerabilities is the first step. You use tools to find potential security flaws. These tools scan your systems for known weaknesses.
- Use automated scanners for efficiency.
- Ensure your scanners are up-to-date with the latest vulnerabilities.
Run scans during off-peak hours to avoid disrupting daily operations. Always get permission before starting your scans. This ensures you follow ethical guidelines.
Analyzing Findings
After scanning, analyze your findings. This step helps you understand the severity of each vulnerability.
- Categorize vulnerabilities based on risk.
- Prioritize fixes for high-risk vulnerabilities first.
Use a table to organize your findings:
| Vulnerability | Risk Level | Recommended Action |
|---|---|---|
| SQL Injection | High | Sanitize inputs |
| Cross-Site Scripting | Medium | Encode outputs |
Document every finding in detail. This documentation helps in tracking and fixing vulnerabilities.
Documenting Results
Performing a vulnerability assessment ethically requires meticulous documentation. Documenting results ensures transparency, accountability, and aids in future assessments. This section delves into the key aspects of documenting results efficiently.
Creating Detailed Reports
Detailed reports are essential for understanding vulnerabilities. They provide a clear picture of the security landscape. A well-structured report should include:
- Summary of findings: A brief overview of identified vulnerabilities.
- Detailed descriptions: Information about each vulnerability, including severity and impact.
- Evidence: Screenshots, logs, or any other proof of the vulnerabilities.
- Remediation steps: Suggested actions to fix the vulnerabilities.
Here is a simple structure for a detailed report:
| Section | Content |
|---|---|
| Introduction | Purpose of the assessment and scope. |
| Summary of Findings | Key vulnerabilities identified. |
| Detailed Analysis | In-depth information on each vulnerability. |
| Evidence | Supporting documentation and screenshots. |
| Remediation | Steps to fix the vulnerabilities. |
Communicating With Stakeholders
Effective communication with stakeholders is crucial. They need to understand the severity and impact of the findings. Use simple language free of technical jargon. Ensure your communication is clear and concise.
Here are some tips for effective communication:
- Use visuals: Charts and graphs can simplify data.
- Be honest: Clearly state the risks and impacts.
- Provide context: Explain why certain vulnerabilities are critical.
- Offer solutions: Suggest practical remediation steps.
Regular updates to stakeholders foster trust and transparency. Always be ready to answer their questions and address concerns.
Mitigating Identified Vulnerabilities
After identifying vulnerabilities, the next step is to mitigate them. Proper mitigation ensures your system remains secure. This section will cover how to prioritize issues and implement solutions.
Prioritizing Issues
Not all vulnerabilities carry the same risk. It’s essential to prioritize them. Use a scoring system like CVSS (Common Vulnerability Scoring System). This helps in identifying which vulnerabilities need immediate attention.
| Priority Level | Description |
|---|---|
| High | Critical vulnerabilities that can cause severe damage. |
| Medium | Vulnerabilities that can cause moderate damage. |
| Low | Vulnerabilities that cause minor damage. |
Focus on high-priority issues first. These can lead to significant security breaches. Medium and low-priority issues should follow. This structured approach ensures efficient resource allocation.
Implementing Solutions
Once you prioritize, the next step is to implement solutions. Solutions vary based on the type of vulnerability. Here are some common methods:
- Patching: Apply updates to fix security flaws.
- Configuration Changes: Adjust settings to enhance security.
- Access Controls: Limit user permissions to minimize risk.
- Monitoring: Continuously watch for suspicious activity.
Each solution must be carefully tested. This ensures it doesn’t introduce new issues. Document every change made. This practice helps in future audits and assessments.
Regularly review and update your mitigation strategies. The threat landscape is always evolving. Staying proactive is key to maintaining security.
Credit: thehackertips.com
Post-assessment Activities
After completing a vulnerability assessment, ethical post-assessment activities are crucial. These steps ensure that identified vulnerabilities are addressed effectively. They also help in planning for future assessments.
Reviewing The Process
Reviewing the assessment process helps in understanding what worked well and what didn’t. This review includes examining the tools used, the scope of the assessment, and the identified vulnerabilities.
- Identify successful methods and tools.
- Document any challenges faced during the assessment.
- Evaluate the accuracy of the findings.
A detailed review helps in refining future assessments. It also ensures that any missed vulnerabilities can be addressed promptly.
Planning For Future Assessments
Planning for future assessments is essential for continuous improvement. Use the insights gained from the review to enhance future assessments.
- Set clear objectives for the next assessment.
- Update the assessment scope based on previous findings.
- Ensure the use of the latest tools and techniques.
Regular assessments help maintain a robust security posture. They ensure that new vulnerabilities are identified and mitigated promptly.
Best Practices For Ethical Assessments
Performing a vulnerability assessment ethically is crucial. It ensures that the process is conducted with integrity and respect for all involved. Following best practices helps maintain trust and security.
Maintaining Confidentiality
Confidentiality is a cornerstone of ethical vulnerability assessments. Sensitive information must be protected at all times.
- Use encryption for storing and transmitting data.
- Limit access to assessment results to authorized personnel only.
- Implement non-disclosure agreements (NDAs) to safeguard information.
Always inform the client about the importance of confidentiality. Make sure they understand the measures in place.
Continuous Learning
Ethical assessors must stay updated with the latest trends and techniques. This ensures accurate and effective assessments.
- Attend workshops and training sessions regularly.
- Read industry publications and research papers.
- Join professional networks and communities for knowledge sharing.
Continuous learning helps identify new vulnerabilities and improve assessment skills. This commitment to growth enhances the overall security posture.

Credit: www.fiverr.com
Frequently Asked Questions
What Is A Vulnerability Assessment?
A vulnerability assessment identifies and quantifies security vulnerabilities in a system. It helps understand potential weaknesses and threats. This process is crucial for maintaining cybersecurity.
Why Is Ethical Vulnerability Assessment Important?
Ethical vulnerability assessments ensure compliance with legal standards. They prevent unauthorized access and data breaches. Ethical practices build trust and protect sensitive information.
How Often Should Vulnerability Assessments Be Conducted?
Vulnerability assessments should be conducted regularly. Ideally, perform assessments quarterly or after significant changes. Regular checks help maintain security posture.
What Tools Are Used For Vulnerability Assessment?
Common tools include Nessus, OpenVAS, and Qualys. These tools scan systems for vulnerabilities. They provide detailed reports for remediation.
Conclusion
Performing a vulnerability assessment ethically ensures system security and builds trust. Follow best practices and stay updated. Document findings clearly and responsibly. Regular assessments help prevent potential threats. Ethical behavior in assessments fosters a secure digital environment. Always prioritize ethical considerations in vulnerability assessments for long-term security benefits.



Leave a Reply