To prepare for a penetration testing engagement, define the scope and objectives clearly. Gather relevant documentation and ensure all stakeholders are informed.
Penetration testing is vital for identifying vulnerabilities in your systems. This proactive approach helps organizations strengthen their security posture. Proper preparation sets the stage for an effective assessment. Begin by defining what assets need testing and understanding the testing boundaries.
Collaborate with your team to gather necessary documentation, such as network diagrams and security policies. Engaging all stakeholders ensures everyone is aligned and aware of the process. This transparency fosters a smooth engagement and enhances the overall effectiveness of the test. By investing time in preparation, you maximize the benefits of the penetration testing effort.
Introduction To Penetration Testing
Penetration testing, or pen testing, simulates real cyber attacks. It helps organizations find and fix vulnerabilities. This process improves overall security. Understanding pen testing is essential for any business.
Setting The Stage For Security Analysis
Before starting a pen test, preparation is crucial. This phase sets the foundation for a successful engagement. Key elements to consider include:
- Defining Scope: Identify what systems will be tested.
- Establishing Rules: Set boundaries for the test.
- Gathering Resources: Ensure all tools and personnel are ready.
Document these elements clearly. This documentation guides the testing team. It also ensures everyone understands their roles.
Importance Of Pen Testing In Cybersecurity
Penetration testing plays a vital role in cybersecurity. It helps identify weak spots in a system. Here are some reasons why it is important:
| Benefit | Description |
|---|---|
| Risk Assessment | Find and evaluate security risks effectively. |
| Compliance | Meet regulatory requirements and standards. |
| Improved Defense | Strengthen security measures based on findings. |
Regular pen testing is essential. It keeps your systems safe from threats. Remember, a proactive approach is always better than a reactive one.
Credit: www.chegg.com
Goal Setting For Penetration Testing
Setting clear goals is essential for a successful penetration testing engagement. Goals guide the entire process. They help teams focus on what matters most. A well-defined goal ensures that resources are used effectively.
Defining The Scope Of Engagement
Scope defines the boundaries of the penetration test. It outlines what will be tested and what will not. A clear scope prevents misunderstandings. Here are key elements to consider:
- Assets: Specify which systems and networks will be tested.
- Exclusions: Identify any areas that should not be tested.
- Testing Types: Decide on black-box, white-box, or gray-box testing.
- Time Frame: Set a clear timeline for the engagement.
Creating a detailed scope document is crucial. This document serves as a reference throughout the engagement. It ensures all parties agree on the objectives.
Identifying Specific Objectives
Specific objectives provide direction to the testing team. They help in measuring success. Here are common objectives for penetration testing:
- Find vulnerabilities in systems and applications.
- Assess the effectiveness of security controls.
- Test incident response capabilities.
- Identify areas for improvement in security posture.
Each objective should be clear and measurable. For example, instead of saying “improve security,” specify “reduce vulnerabilities by 30%.” This clarity helps teams focus on achieving tangible results.
Setting goals and defining the scope ensures a successful engagement. A focused approach leads to better security outcomes.
Assembling The Pen Testing Team
Assembling a skilled team is crucial for successful penetration testing. The right experts help uncover vulnerabilities effectively. Focus on the skill sets and collaboration needed for the engagement.
Selecting The Right Skill Set
Choose team members with diverse skills. Each member should bring unique strengths.
- Security Analysts: Identify and analyze security risks.
- Network Engineers: Understand network architecture and protocols.
- Application Developers: Assess application vulnerabilities.
- Compliance Experts: Ensure adherence to standards and regulations.
Consider these essential skills:
| Skill | Description |
|---|---|
| Penetration Testing | Simulate attacks to find weaknesses. |
| Social Engineering | Test human factors in security. |
| Cryptography | Understand data protection methods. |
| Risk Management | Evaluate and prioritize security risks. |
Building A Collaborative Team
Teamwork is vital for effective penetration testing. Foster open communication among members.
- Schedule regular meetings to discuss progress.
- Encourage sharing of ideas and strategies.
- Use collaboration tools for better coordination.
Establish clear roles:
- Lead Tester: Oversees the testing process.
- Data Analyst: Analyzes findings and reports.
- Client Liaison: Communicates with stakeholders.
A strong, collaborative team enhances overall results. Build trust and respect among members.

Credit: peoplelogyscholarship.com
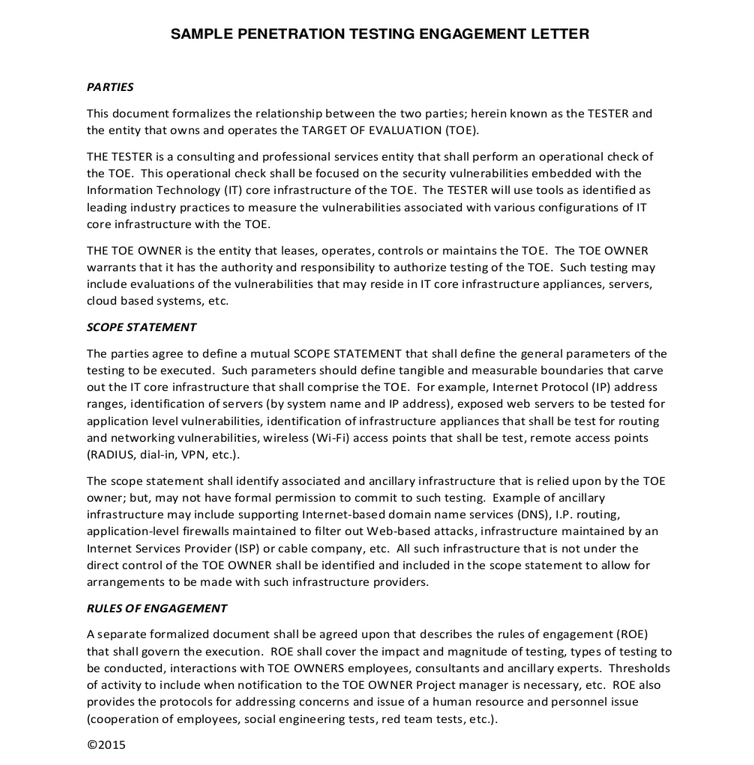
Legal Considerations And Permissions
Preparing for a penetration testing engagement involves several legal considerations. Proper permissions and compliance are essential. They protect both the tester and the organization. Without them, the testing could lead to legal issues.
Understanding Compliance Requirements
Many industries have strict rules about data security. Understanding these requirements helps in planning the test. Here are some common regulations:
| Regulation | Description |
|---|---|
| GDPR | Regulates data protection in the EU. |
| HIPAA | Protects health information in the USA. |
| PCI DSS | Secures credit card transactions globally. |
Review these regulations to ensure compliance. Non-compliance can lead to heavy fines.
Obtaining Necessary Authorizations
Before starting a penetration test, obtain proper authorizations. This is crucial for legal protection. Follow these steps to get the necessary permissions:
- Identify Stakeholders: Know who needs to approve the test.
- Draft a Permission Letter: Clearly outline the scope and objectives.
- Set Boundaries: Specify what is and isn’t allowed during the test.
- Get Signatures: Ensure all stakeholders sign the document.
Always keep copies of the authorization documents. They serve as proof of permission and help avoid misunderstandings.
Technical Preparation
Technical preparation is crucial for successful penetration testing. It ensures the testing team operates effectively. Proper setup helps identify vulnerabilities accurately. Follow these steps to prepare technically.
Gathering Intelligence
Intelligence gathering is the first step in penetration testing. This phase involves collecting data about the target system. Use various techniques to gather information.
- Footprinting: Discover basic information about the target.
- Scanning: Identify open ports and services.
- Enumeration: Extract detailed information about user accounts and services.
Utilize tools like:
| Tool | Purpose |
|---|---|
| nmap | Network scanning and enumeration |
| Maltego | Graphical link analysis tool |
| Recon-ng | Web reconnaissance framework |
Document all findings carefully. This information is vital for later stages.
Setting Up The Testing Environment
Setting up the testing environment is essential. Create a controlled setting for the tests. This includes hardware, software, and tools.
- Choose a safe network: Use a separate network for testing.
- Install required tools: Ensure all necessary software is ready.
- Configure systems: Set up systems to reflect real-world conditions.
Consider using virtual machines. They provide a safe space to conduct tests. Always have a backup plan.
Remember to communicate with your team. Clear communication helps avoid confusion. Keep everyone updated about changes in the environment.
Strategizing The Attack Plan
Preparing for a penetration testing engagement requires a solid attack plan. This plan helps identify weaknesses in your system. Effective strategies increase the chance of discovering vulnerabilities. Each step must be clear and focused. Aim for a systematic approach to ensure thorough testing.
Choosing The Testing Methods
Selecting the right testing methods is crucial. Different methods target various aspects of a system. Here are some common penetration testing methods:
- Black Box Testing: No prior knowledge of the system.
- White Box Testing: Complete access to system details.
- Gray Box Testing: Limited knowledge of the system.
Choose methods based on your goals. Consider the depth of testing needed. Some methods might require more resources. Others might be quicker to implement. Always align methods with business objectives.
Prioritizing Targets And Vulnerabilities
Identifying targets and vulnerabilities is essential. Focus on critical assets first. This ensures the most important areas are tested thoroughly. Use the following criteria to prioritize:
- Asset Value: Identify the most valuable assets.
- Threat Landscape: Understand potential threats.
- Vulnerability Severity: Rate vulnerabilities based on risk.
Consider using a table for better clarity:
| Asset | Value | Threat Level | Vulnerability Severity |
|---|---|---|---|
| Database | High | Critical | High |
| Web Server | Medium | Medium | Medium |
| Internal Network | Low | Low | Low |
Regularly review and update your priorities. This helps adapt to new threats and changes in your environment. Effective prioritization leads to successful penetration testing.
Execution Of Penetration Tests
Executing penetration tests involves careful planning and structured steps. Each phase helps identify weaknesses in your system. This section covers how to conduct tests and document findings effectively.
Conducting The Tests
Conducting penetration tests requires a systematic approach. Follow these essential steps:
- Define the Scope: Determine which systems and applications to test.
- Choose the Testing Methodology: Select from black box, white box, or gray box testing.
- Gather Information: Collect data about the target system.
- Identify Vulnerabilities: Use tools to find weaknesses in the system.
- Exploit Vulnerabilities: Attempt to gain unauthorized access to the system.
- Cleanup: Ensure no changes remain post-testing.
Documenting Findings
Documenting findings is crucial for future reference. Use clear and concise language. Include the following key elements:
| Element | Description |
|---|---|
| Executive Summary | High-level overview for stakeholders. |
| Technical Details | In-depth analysis of vulnerabilities found. |
| Recommendations | Specific actions to mitigate risks. |
| Appendices | Include additional data and resources. |
Ensure your documentation is organized and easy to read. Use bullet points for clarity. Highlight critical vulnerabilities and their potential impact.
Reporting And Follow-up
After a penetration testing engagement, effective reporting and follow-up are crucial. These steps ensure that vulnerabilities are addressed and security improves over time.
Creating A Comprehensive Report
A thorough report outlines findings and recommendations. It should be clear and structured. Here are key elements to include:
- Executive Summary: Summarize key findings for non-technical stakeholders.
- Methodology: Describe the testing process and tools used.
- Findings: List vulnerabilities discovered during testing.
- Severity Ratings: Classify vulnerabilities by risk level.
Use tables for clarity. Here’s an example:
| Vulnerability | Severity | Description |
|---|---|---|
| SQL Injection | High | Allows attackers to manipulate database queries. |
| Cross-Site Scripting (XSS) | Medium | Enables scripts to run in users’ browsers. |
| Weak Passwords | Low | Simple passwords can be easily guessed. |
A well-organized report helps stakeholders understand the security posture. Use visuals to highlight critical information.
Recommending Remedial Actions
After identifying vulnerabilities, recommend actions to fix them. Clear recommendations guide teams in addressing issues. Consider these steps:
- Prioritize Vulnerabilities: Focus on high-severity issues first.
- Provide Solutions: Suggest specific fixes for each vulnerability.
- Offer Best Practices: Recommend security measures and policies.
Ensure that recommendations are actionable and realistic. This helps teams implement fixes efficiently. Always follow up after the report is delivered. Check if the team understands the findings.
Regular follow-ups ensure that vulnerabilities are addressed. This builds a stronger security posture.
Post-engagement Actions
After a penetration testing engagement, the focus shifts to actionable steps. Proper post-engagement actions can enhance your security posture. This phase includes analyzing findings and planning improvements.
Conducting A Debriefing Session
A debriefing session is crucial for understanding test results. Gather your team and the testing firm. Discuss findings in detail.
- Identify vulnerabilities: Review all discovered weaknesses.
- Discuss methodology: Understand how tests were conducted.
- Clarify findings: Ask questions on unclear points.
Document key takeaways. Use this information to inform your security strategy.
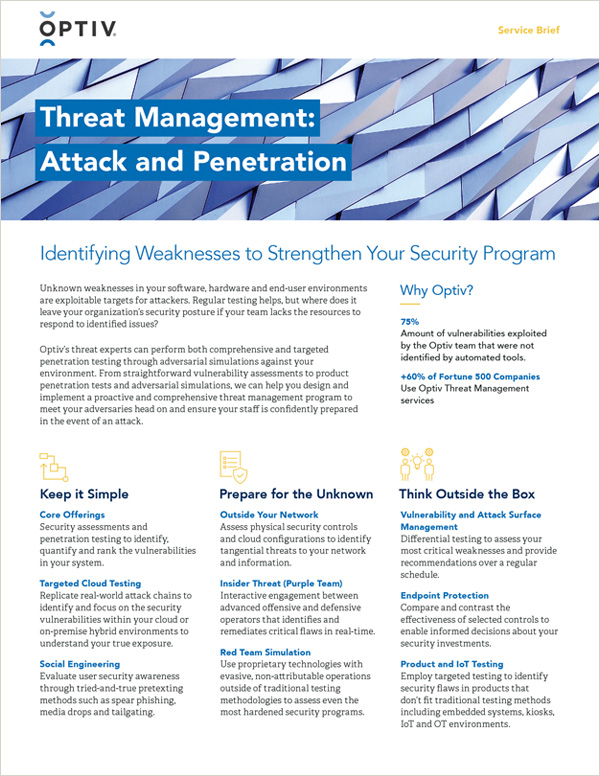
Planning For Future Security Measures
After understanding vulnerabilities, it’s time to plan. Implement changes to strengthen security. Consider these steps:
- Patch vulnerabilities: Fix all identified issues immediately.
- Enhance training: Educate employees on security best practices.
- Update policies: Revise security policies based on findings.
- Schedule regular tests: Plan future penetration tests to stay ahead.
These actions help maintain a robust security framework. Continuous improvement is key to safeguarding your systems.
Credit: www.optiv.com
Frequently Asked Questions
What Is Penetration Testing?
Penetration testing is a simulated cyber attack on your system. It helps identify vulnerabilities before malicious hackers exploit them. By mimicking real-world attacks, organizations can strengthen their defenses. This proactive approach enhances security and compliance, providing peace of mind.
How Should I Prepare For Penetration Testing?
Preparation involves gathering documentation and defining scope. Ensure all stakeholders understand the process and objectives. Inform your team about the test schedule and expected outcomes. Reviewing existing security measures can also help identify areas needing attention. This sets the stage for a successful engagement.
What Documentation Is Needed For Penetration Testing?
Key documentation includes network diagrams, application architecture, and security policies. Additionally, provide any existing vulnerability assessments and incident response plans. This information helps testers understand your environment better. Clear documentation streamlines the process and enhances the effectiveness of the testing.
How Long Does A Penetration Test Take?
The duration of a penetration test varies based on complexity. Typically, tests can last from a few days to several weeks. Factors include the size of the environment and scope of the assessment. Proper planning ensures timely completion and thorough analysis of findings.
Conclusion
Preparing for a penetration testing engagement is crucial for your organization’s security. A well-structured plan ensures effective testing and valuable insights. By following the steps outlined in this guide, you can enhance your readiness. This proactive approach will help safeguard your assets and strengthen your overall cybersecurity posture.




Leave a Reply