Ethical hacking techniques identify and fix vulnerabilities in network security. These methods help protect sensitive information from cyber threats.
Ethical Hacking Techniques for Network Security:Ethical hacking, often called penetration testing, plays a crucial role in network security. It involves simulating cyber attacks to identify and remedy security flaws. Ethical hackers use various techniques such as vulnerability scanning, social engineering, and penetration testing. These professionals ensure that networks are robust and resilient against potential threats.
Employing ethical hackers helps organizations stay ahead of cybercriminals. Regular assessments and continuous monitoring are essential for maintaining network integrity. Effective ethical hacking fortifies network defenses and safeguards sensitive data. This proactive approach is vital for any organization aiming to secure its digital assets.
Introduction To Ethical Hacking
Ethical hacking helps protect networks from bad hackers. Ethical hackers find and fix security holes. This keeps data and systems safe.
What Is Ethical Hacking?
Ethical hacking means finding and fixing security problems. Ethical hackers use the same methods as bad hackers. But they help companies stay safe.
Importance In Network Security
Network security is very important. Networks hold sensitive data. Ethical hacking helps protect this data. Without it, hackers can steal information.
- Identifies weak spots in the network
- Prevents data breaches
- Ensures compliance with regulations
| Benefit | Description |
|---|---|
| Security Assessment | Finds and fixes security holes |
| Data Protection | Keeps sensitive data safe |
| Compliance | Ensures rules are followed |
Types Of Ethical Hacking
Ethical hacking is essential for network security. Different hackers use different techniques. Let’s explore three main types: White Hat, Black Hat, and Gray Hat Hackers.
White Hat Hackers
White Hat Hackers are the good guys. They protect systems and networks. They work with organizations to find and fix vulnerabilities.
- Use legal methods
- Follow ethical guidelines
- Help improve security
White Hat Hackers use tools like penetration testing. They identify weaknesses and secure systems.
Black Hat Hackers
Black Hat Hackers are the bad guys. They break into systems without permission. Their goal is to steal data or cause harm.
- Use illegal methods
- Ignore ethical guidelines
- Cause damage or steal information
Black Hat Hackers use malware and exploit vulnerabilities. Their actions are harmful and illegal.
Gray Hat Hackers
Gray Hat Hackers fall in between. They don’t have permission but don’t harm systems. They find vulnerabilities and report them.
- Use semi-legal methods
- Don’t follow strict ethical guidelines
- Sometimes help, sometimes harm
Common Hacking Techniques
Network security is crucial in our digital world. Understanding common hacking techniques helps protect systems. Let’s explore three major techniques hackers use.
Phishing
Phishing is a popular hacking method. Hackers trick people into giving personal information. They usually send fake emails that look real.
- Emails often contain malicious links.
- They may ask for passwords or credit card details.
- Victims think the email is from a trusted source.
Be cautious of unexpected emails. Check the sender’s address carefully. Never click on suspicious links.
Sql Injection
SQL Injection is a technique used to exploit databases. Hackers insert malicious SQL code into input fields.
| Action | Result |
|---|---|
| Insert code | Gain unauthorized access |
| Modify database | Steal or delete data |
Secure input fields to prevent SQL injections. Use prepared statements and parameterized queries.
Denial Of Service
Denial of Service (DoS) attacks overload systems. The goal is to make a website or service unavailable.
- Attackers send massive amounts of traffic.
- Servers get overwhelmed and crash.
- Legitimate users cannot access the service.
Implement measures to detect and mitigate DoS attacks. Use firewalls and load balancers to manage traffic.
Understanding these techniques helps in building strong network security. Stay informed and vigilant.
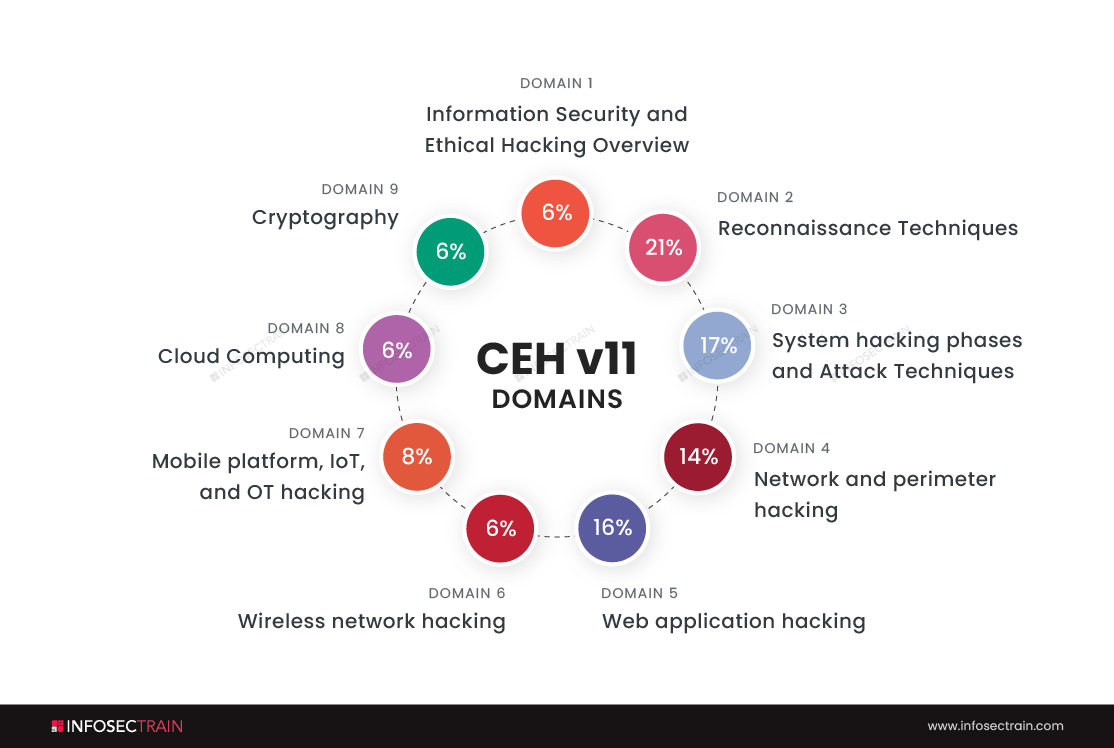
Credit: www.infosectrain.com
Network Security Basics
Understanding the basics of network security is crucial in protecting data. Ethical hacking techniques help identify and fix vulnerabilities. Let’s explore some fundamental aspects.
Firewalls
Firewalls act as a barrier between your network and potential threats. They filter incoming and outgoing traffic based on security rules. Firewalls can be hardware, software, or a combination of both.
- Packet Filtering Firewalls: Check packets of data against a set of rules.
- Stateful Inspection Firewalls: Track the state of active connections and make decisions based on the context of the traffic.
- Proxy Firewalls: Act as an intermediary between users and the internet.
Intrusion Detection Systems
Intrusion Detection Systems (IDS) monitor network traffic for suspicious activity. They alert administrators about potential threats. IDS can be network-based or host-based.
| Type | Description |
|---|---|
| Network-Based IDS | Monitors network traffic for multiple devices. |
| Host-Based IDS | Monitors traffic and system activities on a single device. |
IDS can detect various attack signatures and anomalies. They play a key role in network security.
Encryption
Encryption ensures that data remains secure during transmission. It converts readable data into an unreadable format. Only authorized parties can decrypt and access the information.
- Symmetric Encryption: Uses the same key for encryption and decryption.
- Asymmetric Encryption: Uses a pair of keys – one for encryption and another for decryption.
Encryption helps protect sensitive data from eavesdroppers and cybercriminals. It’s an essential part of maintaining network security.
Penetration Testing
Penetration testing is a vital part of ethical hacking. It helps identify security weaknesses in a network. This method simulates a cyber attack to find vulnerabilities. By doing so, organizations can strengthen their network security.
Planning And Reconnaissance
Planning is the first step in penetration testing. It’s crucial to define the scope and goals. This helps to focus the test on specific areas of the network.
Reconnaissance, also known as information gathering, comes next. Ethical hackers collect data about the target system. They look for IP addresses, domain names, and other details.
- Define scope
- Set goals
- Gather IP addresses
- Collect domain names
Scanning And Enumeration
In the scanning phase, ethical hackers use various tools. They identify open ports and services. This helps to find potential entry points into the network.
Enumeration involves listing all resources and services. Hackers look for user accounts, directories, and network shares. This information is crucial for the next phase.
| Tools | Purpose |
|---|---|
| Nmap | Port scanning |
| Netcat | Banner grabbing |
Exploitation
Exploitation is the final phase of penetration testing. Ethical hackers use the information gathered to exploit vulnerabilities. This could involve gaining unauthorized access or extracting sensitive data.
It’s important to note that the goal is not to cause damage. Instead, it is to identify and fix security weaknesses.
- Identify vulnerabilities
- Exploit weaknesses
- Report findings
Exploitation is a critical step. It helps to understand how attackers might breach the network. This knowledge is used to strengthen defenses.

Credit: www.amazon.com
Tools For Ethical Hacking
Ethical hacking relies on various tools. These tools help to find and fix vulnerabilities. They are essential for network security. Let’s explore some important tools used by ethical hackers.
Kali Linux
Kali Linux is a powerful tool for ethical hackers. It is a Linux-based operating system. It comes with many pre-installed security tools.
- Free and Open Source
- Over 600 Security Tools
- Supported by a Large Community
Kali Linux is user-friendly. It is designed for penetration testing. Hackers use it to test and secure networks.
Metasploit
Metasploit is a popular tool for penetration testing. It helps find vulnerabilities in systems. It also helps exploit them to test security.
| Feature | Description |
|---|---|
| Exploit Modules | Over 1,500 modules available |
| Payloads | Delivers malicious code safely |
| Community Support | Active and engaged community |
Metasploit is user-friendly. It helps ethical hackers conduct tests efficiently.
Wireshark
Wireshark is a network protocol analyzer. It captures and analyzes network traffic. It is essential for network troubleshooting.
- Captures live network data
- Filters and views packets in detail
- Supports multiple protocols
Wireshark is used globally. It helps find issues in network communications. It is a key tool for network security.
Legal And Ethical Considerations
Ethical hacking aims to identify and fix security vulnerabilities. Hackers must follow legal and ethical guidelines. Breaking these rules can lead to serious consequences. Below, we discuss important aspects of these considerations.
Laws And Regulations
Several laws govern ethical hacking activities. These laws vary by country. It is crucial to understand these regulations before starting any hacking activity.
- Computer Fraud and Abuse Act (CFAA): This U.S. law criminalizes unauthorized access to computer systems.
- General Data Protection Regulation (GDPR): This European law protects data privacy and affects how data is handled.
- Cybersecurity Information Sharing Act (CISA): This U.S. law encourages sharing of cybersecurity information between government and private sectors.
Code Of Conduct
Ethical hackers should adhere to a strict code of conduct. This ensures their actions are both legal and ethical.
- Permission: Always obtain written permission before performing any tests.
- Confidentiality: Protect sensitive information at all times.
- Integrity: Do not exploit vulnerabilities for personal gain.
- Reporting: Report all findings honestly and accurately.
Adhering to these guidelines helps maintain trust and credibility. It also ensures the security of the systems being tested.
Future Of Ethical Hacking
The future of ethical hacking is bright. It plays a key role in network security. As technology evolves, so do threats. Ethical hackers must stay ahead. They protect sensitive data and systems. This section explores emerging trends and career opportunities.
Emerging Trends
New trends in ethical hacking are shaping the industry. These trends include:
- AI and Machine Learning: Ethical hackers use AI to predict threats.
- Cloud Security: Securing cloud environments is now crucial.
- IoT Security: Protecting smart devices is a growing focus.
- Zero Trust Security: This model assumes no trust and verifies every access.
| Trend | Description |
|---|---|
| AI and Machine Learning | Predict and detect threats faster. |
| Cloud Security | Ensure data safety in cloud services. |
| IoT Security | Protect interconnected smart devices. |
| Zero Trust Security | Verify every access, trust no one. |
Career Opportunities
Ethical hacking offers many career opportunities. These roles are in high demand:
- Penetration Tester: They find and exploit system vulnerabilities.
- Security Analyst: They monitor systems and detect threats.
- Security Consultant: They advise organizations on security practices.
- Incident Responder: They manage and mitigate security breaches.
These roles require a blend of skills. Technical know-how and problem-solving are key. Companies seek certified professionals. Training and certification boost career prospects.

Credit: www.mimecast.com
Frequently Asked Questions
What Is Ethical Hacking?
Ethical hacking involves authorized attempts to gain unauthorized access to computer systems. It’s done to identify security vulnerabilities. Ethical hackers use the same techniques as malicious hackers but with permission.
Why Is Network Security Important?
Network security is crucial to protect sensitive data from unauthorized access. It prevents data breaches and cyber-attacks. Effective security measures ensure the confidentiality, integrity, and availability of data.
What Are Common Ethical Hacking Techniques?
Common techniques include penetration testing, vulnerability scanning, and social engineering. These methods help identify and fix security weaknesses. Ethical hackers use these techniques to improve network defenses.
How Can Penetration Testing Improve Security?
Penetration testing simulates cyber-attacks to find vulnerabilities in systems. It helps organizations fix security issues before malicious hackers exploit them. Regular tests enhance overall security posture.
Conclusion
Mastering ethical hacking techniques is crucial for robust network security. These practices help identify and mitigate vulnerabilities efficiently. Embrace these methods to protect sensitive data and maintain trust. Stay updated with the latest tools and strategies. Prioritize ethical hacking to ensure a safer digital environment for everyone.




Leave a Reply