Author: Wasim Khan Sujon
-

Information Security Policies for Healthcare: Safeguard Tips
Information security policies for healthcare organizations are critical for protecting patient data. These policies ensure compliance with regulations like HIPAA and safeguard sensitive information from breaches. Healthcare organizations face unique challenges in managing sensitive patient information. With increasing cyber threats and stringent regulations, having robust information security policies is essential. These policies outline the procedures
-

Top Cybersecurity Threats to Watch Out for in 2024: Stay Safe!
Top cybersecurity threats to watch out for in 2024 include advanced ransomware attacks and sophisticated phishing schemes. Organizations must prioritize proactive measures to mitigate these risks effectively. As technology evolves, so do the tactics of cybercriminals. In 2024, businesses and individuals face an increasingly complex landscape of cybersecurity threats. Ransomware attacks are becoming more advanced,
-
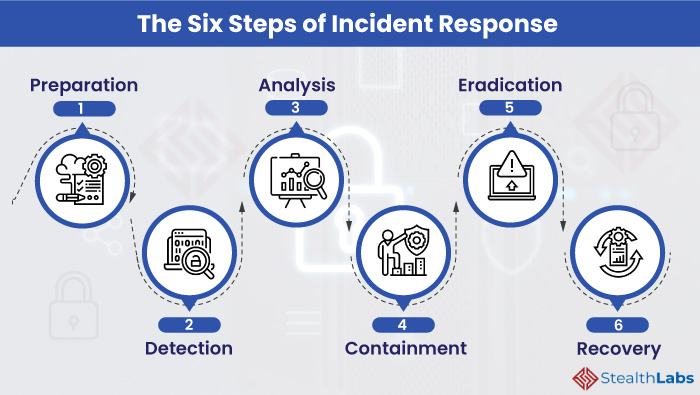
How to Respond to a Cybersecurity Incident: Swift Actions
To respond to a cybersecurity incident, immediately assess the situation and contain the breach. Next, notify relevant stakeholders and begin recovery efforts. How to Respond to a Cybersecurity Incident:Cybersecurity incidents can strike unexpectedly, posing significant risks to businesses and individuals alike. Effective response strategies are essential to minimize damage and recover swiftly. Organizations must develop
-

Cybersecurity Measures: Safeguard Your Online Banking
To protect online banking accounts, use strong, unique passwords and enable two-factor authentication. Regularly monitor account activity and update security software. Cybersecurity Measures:Online banking has revolutionized how we manage finances, offering convenience at our fingertips. However, this ease also brings risks, making cybersecurity crucial. Cyber threats targeting bank accounts are on the rise, from phishing
-

Cybersecurity Compliance Requirements for Healthcare: Essential Guide
Cybersecurity compliance requirements for healthcare organizations primarily include HIPAA, HITECH, and GDPR regulations. These regulations ensure the protection of patient data and promote best practices in information security. Healthcare organizations face critical cybersecurity compliance requirements to protect sensitive patient information. These regulations safeguard personal health records and ensure data security. Adhering to frameworks like HIPAA
-

Guide to Conducting a Cybersecurity Risk Assessment: Ensure Safety!
A cybersecurity risk assessment identifies vulnerabilities in your systems and evaluates potential threats. This process helps prioritize security measures and allocate resources effectively. Guide to Conducting a Cybersecurity Risk Assessment:Cybersecurity is critical in today’s digital landscape, where threats evolve constantly. Conducting a risk assessment helps organizations understand their security posture. It involves identifying assets, assessing
-
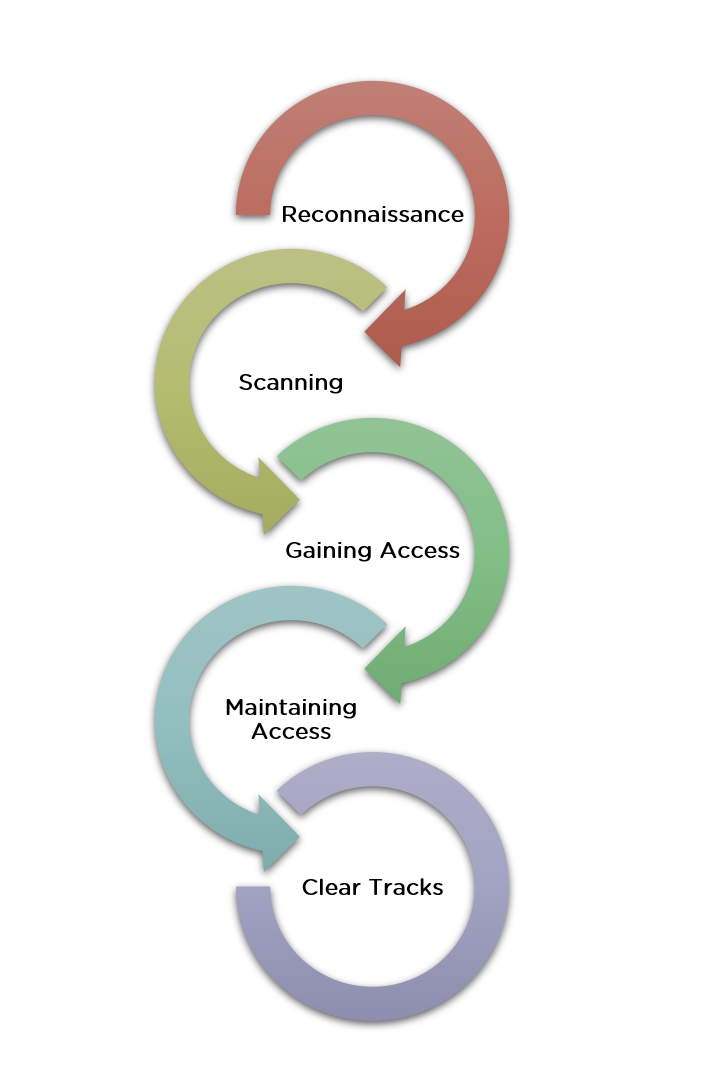
How to Use Nmap for Ethical Hacking: A Step-by-Step Guide
To use Nmap for ethical hacking, install Nmap and run scans to identify open ports and services on a target. Analyze the scan results to assess potential vulnerabilities. How to Use Nmap for Ethical Hacking:Nmap, short for Network Mapper, is a powerful tool used in ethical hacking for network discovery and security auditing. It is
-
How to Perform a Vulnerability Assessment Ethically: Best Practices
To perform a vulnerability assessment ethically, obtain proper authorization and follow a structured methodology. Ensure all findings are reported responsibly. How to Perform a Vulnerability Assessment Ethically:Vulnerability assessments are crucial for identifying security weaknesses in systems. Conducting these assessments ethically helps maintain trust and legal compliance. Start by securing explicit permission from the organization you
-

Ethical Hacking Courses Online for Free: Boost Your Cyber Skills
Many platforms offer free ethical hacking courses online. These courses help you learn valuable cybersecurity skills. Ethical Hacking Courses Online for Free:Ethical hacking courses provide crucial knowledge to protect digital assets. Aspiring cybersecurity professionals can find numerous free resources online. Platforms like Coursera, Udemy, and Cybrary offer beginner to advanced courses. These programs cover topics
-

Ethical Hacking Vs. Black Hat Hacking: Unmasking the Differences
Ethical hacking involves authorized testing to find security vulnerabilities. Black hat hacking exploits these vulnerabilities for malicious purposes. Ethical Hacking Vs. Black Hat Hacking:Ethical hacking and black hat hacking represent two sides of the cybersecurity spectrum. Ethical hackers, also known as white hat hackers, help organizations by identifying and fixing security flaws. They work legally
