Cybersecurity threats in 2024 include advanced ransomware attacks and increased vulnerabilities in IoT devices. Organizations must prioritize proactive measures to mitigate these risks.
As we navigate through 2024, the landscape of cybersecurity continues to evolve. Cybercriminals are leveraging sophisticated techniques to exploit weaknesses in systems and networks. Ransomware remains a dominant threat, targeting businesses of all sizes and demanding hefty payments. Meanwhile, the rise of Internet of Things (IoT) devices introduces new vulnerabilities, creating additional entry points for attackers.
Companies must stay vigilant and implement robust security protocols to protect sensitive data. Educating employees about cyber hygiene is equally crucial in safeguarding against threats. By understanding and addressing these risks, businesses can better secure their digital environments and maintain customer trust in an increasingly interconnected world.
The Evolving Cyber Threat Landscape
The cyber threat landscape is changing rapidly in 2024. New technologies bring exciting opportunities, but they also create new vulnerabilities. Cybercriminals adapt quickly, using these weaknesses for malicious purposes. Understanding these trends is crucial for everyone, from businesses to individuals.
Emerging Technologies And New Vulnerabilities
Emerging technologies like the Internet of Things (IoT) and 5G networks increase the number of connected devices. Each device can be a potential target for cyberattacks. Here are some common vulnerabilities:
- Weak passwords
- Unpatched software
- Insecure configurations
These vulnerabilities lead to serious risks, including:
- Data breaches
- Financial losses
- Reputational damage
Organizations must prioritize security measures. Regular updates and strong passwords can help protect against these threats.
The Rise Of Ai In Cyber Attacks
Artificial Intelligence (AI) is becoming a tool for cybercriminals. They use AI to automate attacks and make them more effective. Some notable uses of AI in cyberattacks include:
- Phishing: AI can create realistic emails that trick users.
- Malware: Smart malware can adapt to avoid detection.
- DDoS attacks: AI can control multiple devices to overwhelm a target.
These tactics make it harder for traditional defenses to keep up. Organizations need to invest in AI-driven security solutions. This investment can help spot threats faster and respond effectively.

Credit: www.connectwise.com
Key Cybersecurity Threats To Watch In 2024
Cybersecurity in 2024 faces new challenges. Attackers are more creative. Organizations must stay alert. Here are the key threats to watch.
Ransomware Tactics And Targets
Ransomware remains a top threat. Attackers use advanced tactics to maximize impact. They target:
- Healthcare institutions
- Government agencies
- Large corporations
- Educational institutions
Ransomware groups will likely:
- Utilize double extortion methods
- Target backups to increase leverage
- Focus on high-value data
Organizations must implement strong security measures. Regular backups and employee training are essential.
State-sponsored Cyber Warfare
Nation-states are increasing their cyber activities. They aim to disrupt economies and steal data. Common tactics include:
- Espionage
- Infrastructure attacks
- Disinformation campaigns
Vulnerable sectors include:
| Sector | Risk Level |
|---|---|
| Energy | High |
| Finance | High |
| Healthcare | Medium |
Governments must enhance defenses. Collaboration and intelligence sharing are crucial.
Deepfake Technology Abuse
Deepfake technology is evolving rapidly. This poses a unique threat. Cybercriminals can create realistic fake videos and audio. They may use this for:
- Fraud
- Blackmail
- Spreading false information
Organizations must stay informed. Implementing detection tools can help. Training employees on recognizing deepfakes is vital.
Vulnerable Sectors: Who’s At Risk?
Cybersecurity threats are evolving rapidly. Many sectors face increased risks in 2024. Understanding these vulnerable areas helps businesses protect themselves.
Healthcare Industry Challenges
The healthcare industry is a primary target for cyberattacks. Patient data is valuable and sensitive. Cybercriminals exploit vulnerabilities for financial gain.
- Data Breaches: Unauthorized access to patient records.
- Ransomware Attacks: Locking essential data until a ransom is paid.
- IoT Devices: Many devices lack proper security measures.
Healthcare organizations must invest in robust cybersecurity measures. Training staff on security best practices is essential.
Financial Sector Under Siege
The financial sector faces relentless cyber threats. Hackers aim to steal funds and personal data. The impact of these attacks can be devastating.
| Threat Type | Description | Impact |
|---|---|---|
| Phishing | Tricking users into sharing sensitive information. | Loss of funds and trust. |
| Card Skimming | Stealing credit card information from devices. | Financial loss for customers and banks. |
| Denial of Service | Overloading systems to disrupt services. | Service outages and customer frustration. |
Financial institutions must strengthen their defenses. Regular audits and employee training are crucial.
Critical Infrastructure At Crosshairs
Critical infrastructure is vital for society’s functioning. This includes energy, water, and transportation systems. Cyberattacks on these sectors can cause chaos.
- Energy Sector: Attacks can disrupt power grids.
- Water Supply: Contamination can occur due to cyber interference.
- Transportation: Systems can be paralyzed, affecting logistics.
Protecting critical infrastructure is essential for national security. Government and private sectors must collaborate for better security.
Personal Data At Risk: Privacy Concerns
Cybersecurity threats in 2024 put your personal data in danger. Hackers are finding new ways to steal information. Protecting your privacy is more important than ever. Understanding these threats helps you stay safe.
Phishing Scams: A Constant Threat
Phishing scams trick users into sharing personal data. Scammers use emails and messages that appear real.
- Fake emails from trusted sources
- Links to fraudulent websites
- Urgent calls for action
Always check the sender’s address. Look for spelling errors or strange requests. Here are tips to avoid phishing:
- Never click on unknown links.
- Verify the sender before responding.
- Use two-factor authentication.
The Dark Web And Identity Theft
The dark web is a hidden part of the internet. Here, stolen data is bought and sold. Identity theft is a major issue.
| Type of Data | Value on the Dark Web |
|---|---|
| Credit Card Information | $5 – $50 |
| Social Security Numbers | $1 – $20 |
| Login Credentials | $1 – $10 |
Protect your identity with these steps:
- Monitor bank statements regularly.
- Use strong, unique passwords.
- Consider a credit monitoring service.
Cybersecurity is everyone’s responsibility. Stay informed to protect your personal data.
Corporate Cyber Defense Strategies
In 2024, businesses face growing cyber threats. Companies must adopt effective cyber defense strategies. These strategies protect sensitive data and maintain customer trust.
Implementing Robust Security Frameworks
Building a strong security framework is vital for any organization. Here are key components:
- Risk Assessment: Identify potential vulnerabilities.
- Access Controls: Limit access to sensitive data.
- Network Security: Use firewalls and intrusion detection systems.
- Data Encryption: Encrypt data both at rest and in transit.
Companies should regularly update their security policies. Regular audits can uncover gaps. Here’s a simple table outlining best practices:
| Practice | Frequency | Description |
|---|---|---|
| Risk Assessment | Quarterly | Identify new vulnerabilities. |
| Policy Review | Annually | Ensure compliance and relevance. |
| Software Updates | Monthly | Patch security flaws. |
Employee Training And Awareness Programs
Employees are often the first line of defense. Training can reduce human error. Here are effective training strategies:
- Conduct regular training sessions.
- Simulate phishing attacks to test awareness.
- Provide resources for reporting suspicious activity.
Key topics should include:
- Password Management: Use strong, unique passwords.
- Social Engineering: Recognize manipulation tactics.
- Data Handling: Properly handle sensitive information.
Creating a culture of cybersecurity is essential. Encourage employees to stay vigilant. This proactive approach helps in preventing breaches.
Governmental Role In Cybersecurity
Governments play a crucial role in cybersecurity. They create laws and policies to protect citizens. As threats grow, so does the need for effective measures. In 2024, this role becomes even more vital. Governments must adapt to new challenges in the digital world.
Regulations And Compliance Standards
Regulations help set rules for cybersecurity. They ensure organizations meet minimum security requirements. Here are some key regulations:
- GDPR: Protects personal data in Europe.
- HIPAA: Safeguards health information in the U.S.
- CCPA: Gives rights to California residents over their data.
Compliance standards vary by industry. Organizations must follow these standards to avoid penalties. Regular audits help ensure compliance.
| Regulation | Region | Focus Area |
|---|---|---|
| GDPR | Europe | Data Protection |
| HIPAA | United States | Health Information |
| CCPA | California | Consumer Privacy |
International Collaboration And Cyber Diplomacy
Cybersecurity is a global issue. Countries must work together to combat threats. International collaboration strengthens defenses. Here are key aspects of this cooperation:
- Information Sharing: Countries share threat intelligence.
- Joint Exercises: Nations conduct training to prepare for attacks.
- Agreements: Countries form treaties to enhance cooperation.
Cyber diplomacy fosters trust among nations. It helps build a unified front against cyber threats. In 2024, international efforts will be vital for ensuring security.
Innovations In Cybersecurity Measures
Cybersecurity threats are evolving rapidly in 2024. New measures are essential to combat these threats. Innovative technologies are emerging to protect data and systems. Organizations must adopt these advancements to stay secure.
Next-gen Antivirus And Malware Protection
Traditional antivirus software struggles against modern threats. Next-gen antivirus solutions use advanced technologies. They employ machine learning and artificial intelligence.
- Real-Time Threat Detection: Identify threats instantly.
- Behavioral Analysis: Monitor user behavior to find anomalies.
- Cloud-Based Protection: Use the cloud for faster updates and responses.
These solutions adapt to new malware. They learn from each attack. This makes them smarter and faster.
| Feature | Benefit |
|---|---|
| Machine Learning | Improved detection rates |
| Cloud Integration | Faster response times |
| Automated Updates | Always up-to-date protection |
Blockchain For Enhanced Security
Blockchain technology offers unique security benefits. It provides decentralized data storage. This makes data tampering extremely difficult.
- Data Integrity: Ensures data remains unchanged.
- Transparency: All transactions are visible to authorized users.
- Decentralization: Reduces single points of failure.
Organizations can use blockchain for secure transactions. It enhances trust and security across platforms. This innovation is crucial for sensitive data protection.
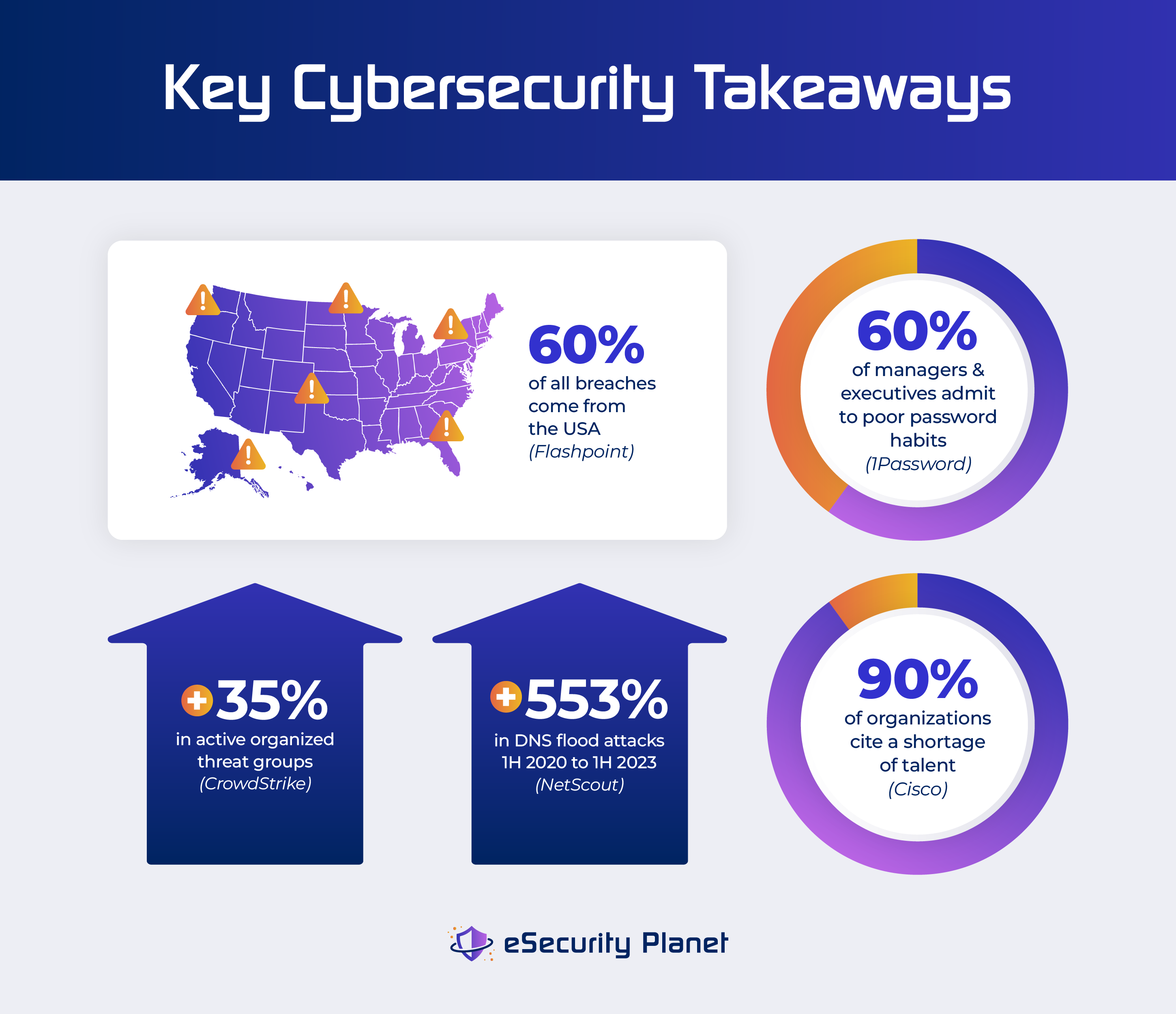
Credit: www.esecurityplanet.com
Preparing For The Inevitable: Response And Recovery
Cybersecurity threats grow every year. Businesses must prepare for attacks. An effective response and recovery plan is crucial. This plan helps minimize damage. It also ensures quick recovery. Let’s explore key components of preparation.
Incident Response Planning
Incident response planning helps organizations react swiftly. A solid plan includes several steps:
- Preparation: Train staff and set up tools.
- Identification: Detect security incidents quickly.
- Containment: Limit damage from the attack.
- Eradication: Remove the threat completely.
- Recovery: Restore systems to normal operations.
- Lessons Learned: Analyze the incident to improve future responses.
Regular updates to the plan are necessary. Use simulations to test the plan. This ensures your team is ready.
Business Continuity And Disaster Recovery
Business continuity and disaster recovery are key to staying operational. These plans focus on maintaining essential functions during crises. Key elements include:
- Risk Assessment: Identify potential threats and impacts.
- Critical Functions: Determine which operations must continue.
- Resource Allocation: Ensure necessary tools and personnel are available.
- Communication Plan: Keep everyone informed during an incident.
Consider using a table for clarity:
| Element | Description |
|---|---|
| Risk Assessment | Identify and evaluate potential threats. |
| Critical Functions | Prioritize essential operations. |
| Resource Allocation | Gather necessary tools and staff. |
| Communication Plan | Inform stakeholders during incidents. |
Regular drills help maintain readiness. Engage your team in these activities. Effective response and recovery save time and money.
Credit: www.code-intelligence.com
Frequently Asked Questions
What Are The Top Cybersecurity Threats In 2024?
In 2024, the leading cybersecurity threats include ransomware attacks, phishing schemes, and IoT vulnerabilities. Ransomware continues to evolve, targeting critical infrastructure. Phishing tactics are becoming more sophisticated, tricking users into revealing sensitive information. Additionally, the proliferation of IoT devices creates new entry points for cybercriminals.
How Can Businesses Prevent Cyber Attacks In 2024?
Businesses can prevent cyber attacks by implementing robust security measures. Regular software updates and strong password policies are essential. Employee training on recognizing phishing attempts is crucial. Utilizing multi-factor authentication adds an extra layer of protection. Finally, conducting regular security audits helps identify vulnerabilities before they are exploited.
What Role Does Ai Play In Cybersecurity Threats?
AI significantly influences cybersecurity threats in 2024. Cybercriminals use AI to automate attacks, making them faster and more efficient. AI can analyze vast amounts of data to identify vulnerabilities. However, it also aids in defense, helping organizations detect threats in real-time.
The ongoing battle between AI attackers and defenders is intensifying.
Are Small Businesses At Risk For Cyber Threats?
Yes, small businesses are increasingly at risk for cyber threats. Many assume they are not targets, making them vulnerable. Cybercriminals often exploit security gaps in smaller organizations. They typically lack robust security measures, making them easier prey. It’s crucial for small businesses to prioritize cybersecurity to protect their assets.
Conclusion
Cybersecurity threats in 2024 pose serious risks for individuals and organizations alike. Staying informed is crucial. Implementing robust security measures can significantly reduce vulnerabilities. Regular updates and employee training are essential. By prioritizing cybersecurity, we can protect valuable data and ensure a safer digital environment for everyone.
Stay vigilant and proactive.




Leave a Reply