To prevent phishing attacks in 2024, use multi-factor authentication and educate employees about recognizing suspicious emails. Regularly update security software to protect against new threats.
How to Prevent Phishing Attacks in 2024:Phishing attacks continue to evolve, targeting both individuals and organizations. As technology advances, cybercriminals become more sophisticated in their tactics, making it essential to stay informed. Understanding the latest phishing trends can help you safeguard sensitive information. Regular training sessions can empower employees to recognize fraudulent messages.
Implementing strong security measures, like multi-factor authentication, adds an extra layer of protection. Keeping software updated also plays a crucial role in defending against these threats. By taking proactive steps, you can significantly reduce the risk of falling victim to phishing scams in 2024. Awareness and vigilance are key in maintaining cybersecurity.

Credit: www.linkedin.com
The Evolving Threat Of Phishing
Phishing attacks are changing quickly. Cybercriminals use smarter methods to trick people. This section explores current trends and predicts future techniques. Understanding these threats helps protect you.
Identifying Current Trends
Phishing attacks now use advanced tactics. Here are some key trends:
- Targeted Phishing: Attackers focus on specific individuals or companies.
- Use of AI: AI generates realistic emails and messages.
- Social Media Phishing: Scammers target users through social platforms.
- SMS Phishing: Text messages trick users into sharing info.
These trends show how phishing is adapting. Awareness is crucial to stay safe.
Predicting Future Phishing Techniques
Phishing will continue to evolve. Here are some predictions:
- Deepfake Technology: Attackers may use deepfake videos to impersonate.
- Increased Personalization: Emails will become more tailored to individuals.
- Voice Phishing: Phone calls may use AI voices to deceive.
- Supply Chain Attacks: Scammers may target trusted vendors.
Staying updated on these techniques is vital. Knowledge is the best defense.
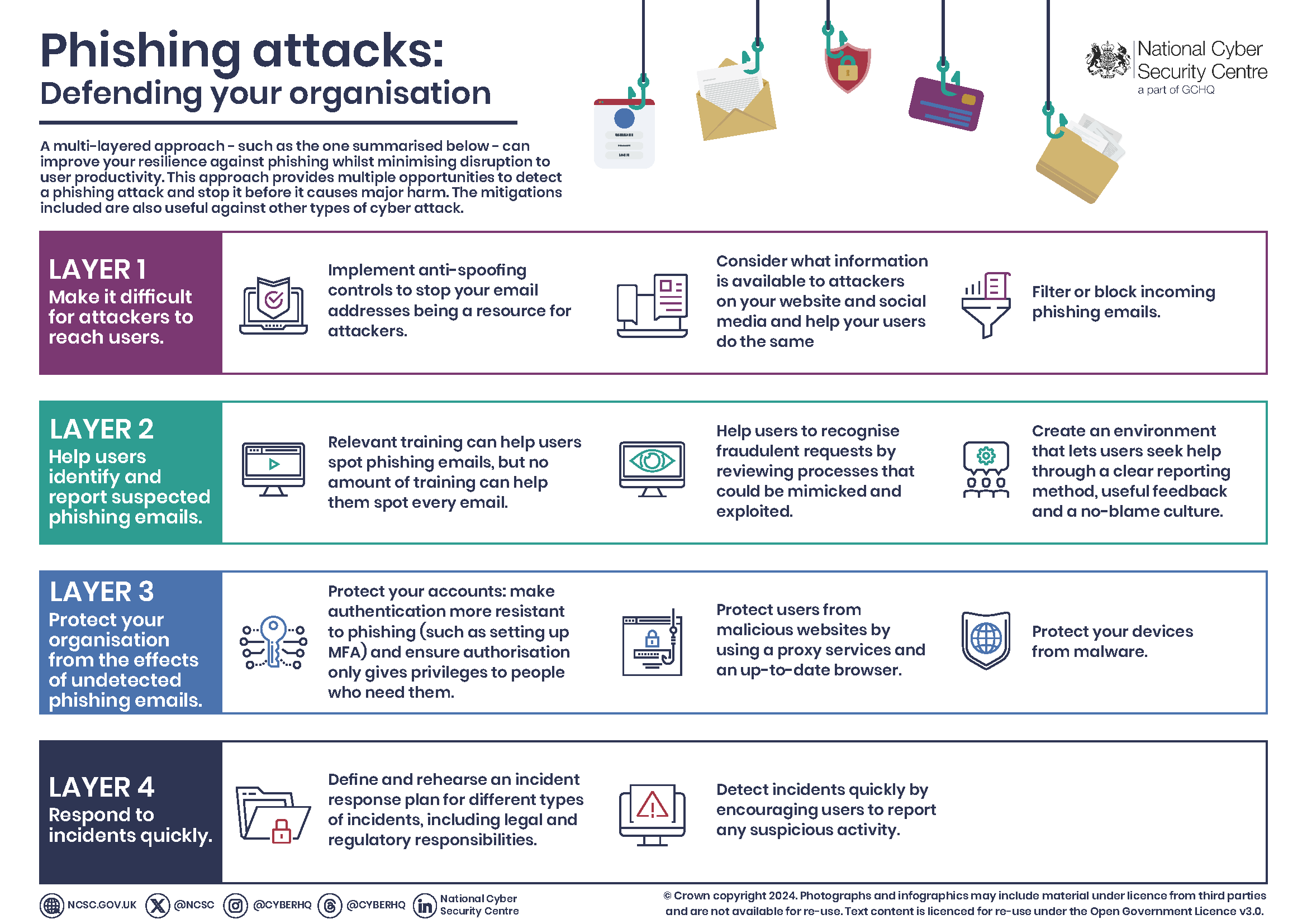
Credit: www.ncsc.gov.uk
Fundamentals Of Phishing Protection
Phishing attacks are a serious threat in 2024. Understanding how to protect yourself is vital. Here are the key fundamentals that everyone should know.
Recognizing Suspicious Emails And Links
Spotting phishing attempts is the first line of defense. Here are some signs to look for:
- Strange sender addresses: Check for misspellings.
- Urgent requests: Be wary of emails asking for immediate action.
- Generic greetings: Legitimate companies use your name.
- Attachments: Avoid opening unexpected files.
Always hover over links before clicking. This shows the real URL. If it looks suspicious, don’t click it.
Importance Of Secure Connections
Using secure connections is crucial for safety. Follow these tips:
- Use HTTPS: Always check for “HTTPS” in the URL.
- Avoid public Wi-Fi: Use a VPN if necessary.
- Keep software updated: Updates fix security holes.
- Enable two-factor authentication: Add an extra layer of security.
Secure connections protect your data. Always prioritize your online safety.
Advanced Security Protocols
In 2024, protecting against phishing attacks requires strong security measures. Advanced security protocols play a key role in this protection. These protocols help to identify and stop phishing attempts effectively. Here are two essential strategies to enhance your security.
Implementing Multi-factor Authentication
Multi-Factor Authentication (MFA) adds an extra layer of security. It requires users to provide two or more verification factors. This makes it harder for attackers to gain access.
- Something you know: A password or PIN.
- Something you have: A mobile device or security token.
- Something you are: Biometric data like fingerprints.
Follow these steps to implement MFA:
- Choose an MFA solution.
- Enable MFA for all accounts.
- Educate users on how to use it.
Deploying Email Filtering Solutions
Email filtering solutions can significantly reduce phishing emails. These tools scan incoming emails for suspicious content. They block harmful messages before they reach your inbox.
Consider these features in email filtering:
| Feature | Benefit |
|---|---|
| Spam Detection | Blocks unwanted emails. |
| Malware Scanning | Detects harmful attachments. |
| Link Protection | Warns about unsafe links. |
Implementing email filters helps to protect your organization. It keeps your inbox safe from phishing threats.
Educational Initiatives For Phishing Awareness
Phishing attacks are on the rise. They target individuals and organizations alike. Effective education can reduce these threats. Training programs are essential for building awareness. Everyone should know how to recognize phishing attempts.
Creating Effective Training Programs
Training programs should be simple and engaging. Here are some key components:
- Interactive Workshops: Hands-on sessions increase retention.
- Regular Updates: Refresh content to include new phishing trends.
- Assessment Tests: Evaluate understanding and identify gaps.
- Incentives: Reward participants for active participation.
Using various formats can enhance learning:
| Format | Description |
|---|---|
| Videos | Short clips explaining phishing tactics. |
| Quizzes | Engaging questions to test knowledge. |
| Case Studies | Real-life examples to analyze. |
Leveraging Real-life Scenarios For Learning
Real-life scenarios enhance understanding. They help individuals relate better to training. Use examples from recent phishing attacks. This makes the threat more tangible.
Incorporate the following methods:
- Role-Playing: Simulate phishing attempts to practice responses.
- Group Discussions: Share experiences and insights on phishing.
- Visual Aids: Use graphics to highlight warning signs.
Encourage participants to report phishing attempts. This builds a proactive culture. Awareness will increase security for everyone.
Leveraging Ai And Machine Learning
Phishing attacks continue to rise, targeting individuals and businesses alike. Using AI and machine learning helps to enhance security measures. These technologies detect and combat phishing attempts more effectively.
Automating Threat Detection
Automating threat detection saves time and resources. Here are key benefits:
- Real-time analysis: AI systems analyze data instantly.
- Pattern recognition: Machine learning identifies suspicious patterns.
- Reduced human error: Automation minimizes mistakes in detection.
Many organizations use AI tools to enhance their security. These tools scan emails and websites for potential threats.
Enhancing Response With Intelligent Systems
Intelligent systems improve the response to phishing attacks. They offer quick solutions to mitigate risks.
| Intelligent System Feature | Benefit |
|---|---|
| Automated alerts | Notifies users of potential threats immediately. |
| Phishing simulations | Trains employees to recognize phishing attempts. |
| Incident response plans | Streamlines the process of handling attacks. |
Implementing these intelligent systems strengthens defenses. Organizations can respond swiftly to threats.

Credit: ironscales.com
Legal And Regulatory Frameworks
Understanding legal frameworks helps in preventing phishing attacks. Laws and regulations shape how organizations protect their data. They also dictate how companies respond to breaches. Staying informed about these frameworks is crucial for businesses.
Understanding Global Anti-phishing Policies
Many countries have enacted laws against phishing. These laws aim to protect consumers and businesses. Below are key international policies:
| Country | Policy Name | Description |
|---|---|---|
| United States | CAN-SPAM Act | Regulates commercial email to combat spam and phishing. |
| European Union | GDPR | Protects personal data and enhances privacy rights. |
| Australia | ACCC Guidelines | Aims to protect consumers from scams and phishing. |
These policies enforce strict penalties for offenders. Organizations must comply to avoid legal repercussions.
Compliance And Best Practices For Businesses
Businesses must adopt best practices to align with regulations. Here are some key strategies:
- Data Protection: Implement strong data encryption methods.
- Employee Training: Conduct regular training sessions on phishing awareness.
- Incident Response Plan: Develop a plan for responding to phishing attacks.
- Regular Audits: Perform audits to ensure compliance with laws.
Staying compliant helps build customer trust. It also minimizes the risk of attacks. Organizations should regularly update their policies. This ensures alignment with evolving regulations.
The Role Of Individual Vigilance
Phishing attacks are on the rise. Every individual plays a crucial role in preventing them. Awareness and actions can stop these scams. Your vigilance matters in 2024.
Personal Security Hygiene
Practice good security habits daily. Here are some tips:
- Use Strong Passwords: Create complex passwords. Use a mix of letters, numbers, and symbols.
- Change Passwords Regularly: Update passwords every three to six months.
- Enable Two-Factor Authentication: Add an extra layer of security.
- Be Cautious with Emails: Always check sender details. Look for spelling errors and strange links.
Understanding what phishing looks like can help. Stay alert to avoid falling for scams.
The Power Of Reporting And Sharing Information
Sharing information helps everyone stay safe. Report phishing attempts immediately. Here’s how:
- Report to Email Providers: Most services have options to report phishing.
- Inform Your Organization: Notify your IT department if you work for a company.
- Educate Others: Share your experiences with friends and family.
Use social media to spread awareness. The more people know, the safer we all are.
Vigilance is key. Protect yourself and others from phishing attacks.
Future-proofing Against Phishing
Protecting yourself from phishing attacks is essential in 2024. Cybercriminals constantly evolve their tactics. Staying ahead requires understanding new technologies and building strong defenses. Here’s how to future-proof your digital life.
Innovations In Cybersecurity Technologies
New technologies emerge to combat phishing. Here are some key innovations:
- AI-Powered Detection: Machine learning identifies phishing attempts quickly.
- Behavioral Analytics: This analyzes user behavior to spot unusual activities.
- Multi-Factor Authentication (MFA): Adds extra security layers to accounts.
- Blockchain Technology: Ensures data integrity and authenticity.
Consider these technologies to enhance your security:
| Technology | Benefit |
|---|---|
| AI-Powered Detection | Quick identification of threats |
| Behavioral Analytics | Detects anomalies in user behavior |
| MFA | Prevents unauthorized access |
| Blockchain | Protects data from tampering |
Building A Resilient Digital Infrastructure
A strong digital infrastructure is vital for security. Here are steps to build resilience:
- Regular Software Updates: Keep software current to fix vulnerabilities.
- Strong Password Policies: Use complex passwords and change them regularly.
- User Education: Train users to recognize phishing attempts.
- Backup Data: Regular backups protect against data loss.
- Incident Response Plan: Prepare for breaches with a clear plan.
Implementing these strategies ensures better protection against phishing. Stay vigilant and proactive in your approach.
Frequently Asked Questions
How Can I Recognize Phishing Emails?
To recognize phishing emails, look for poor grammar and spelling mistakes. Check the sender’s email address; it often resembles a legitimate source but has slight differences. Be wary of urgent requests for personal information. Hover over links to see the actual URL before clicking.
What Are The Signs Of A Phishing Attack?
Common signs of a phishing attack include unexpected emails asking for sensitive information. Look for generic greetings and suspicious attachments. Phishing attempts often create a sense of urgency. Legitimate companies rarely request sensitive data via email, so always verify through official channels.
How Can I Protect Myself From Phishing?
To protect yourself from phishing, use strong, unique passwords for each account. Enable two-factor authentication wherever possible. Regularly update your software and antivirus programs. Be cautious of unsolicited emails and avoid clicking on unknown links or attachments. Educating yourself on phishing tactics is crucial.
What Should I Do If I Fall For Phishing?
If you fall for phishing, immediately change your passwords for affected accounts. Monitor your financial statements for unauthorized transactions. Report the phishing incident to your email provider and relevant authorities. Consider placing a fraud alert on your credit report to prevent identity theft.
Conclusion
Phishing attacks can disrupt personal and professional lives. Staying informed is crucial for prevention. Always verify sources before clicking links. Use strong passwords and enable two-factor authentication. Regularly update your software to protect against vulnerabilities. By adopting these measures, you can significantly reduce the risk of falling victim to phishing scams.




Leave a Reply