Author: Wasim Khan Sujon
-

How to Choose the Right Project Management Software for Your Team: Smart Selection Tips
To choose the right project management software, assess your team’s specific needs and evaluate features that align with those requirements. Consider user-friendliness, integration capabilities, and budget constraints. How to Choose the Right Project Management Software for Your Team:How to Choose the Right Project Management Software for Your TeamSelecting project management software is a critical decision
-

Importance of Encryption Shielding Digital Realms
Encryption is crucial for protecting sensitive data in modern network security systems. It ensures confidentiality, integrity, and authenticity of information. Importance of Encryption Shielding Digital Realms:In today’s digital landscape, data breaches and cyber threats are rampant. Organizations face constant challenges in safeguarding sensitive information. Encryption serves as a robust defense mechanism against unauthorized access and
-

Affordable Network Security Monitoring Tools for Startups: Safeguard Your Data!
Affordable network security monitoring tools for startups include SolarWinds, Sumo Logic, and Zscaler. These solutions offer essential features without breaking the bank. As cyber threats grow, startups must prioritize network security. Many affordable tools cater specifically to the needs of smaller businesses, enabling them to protect sensitive data effectively. These tools often provide real-time monitoring,
-

Best Practices for Small Business Network Security in 2024: Stay Safe!
To ensure robust network security for small businesses in 2024, prioritize regular software updates and employee training. Implement strong passwords and multi-factor authentication to enhance data protection. Best Practices for Small Business Network Security in 2024:As cyber threats continue to evolve, small businesses must adopt effective network security practices. A single breach can lead to
-

Top-Rated Firewall Solutions: Shield Your Corporate Network!
Top-rated firewall solutions for corporate network security include Palo Alto Networks, Fortinet, and Cisco. These options provide robust protection against cyber threats. In today’s digital landscape, corporate network security is paramount. Businesses face increasing threats from cybercriminals, making effective firewall solutions essential. Firewalls serve as the first line of defense, controlling incoming and outgoing traffic
-
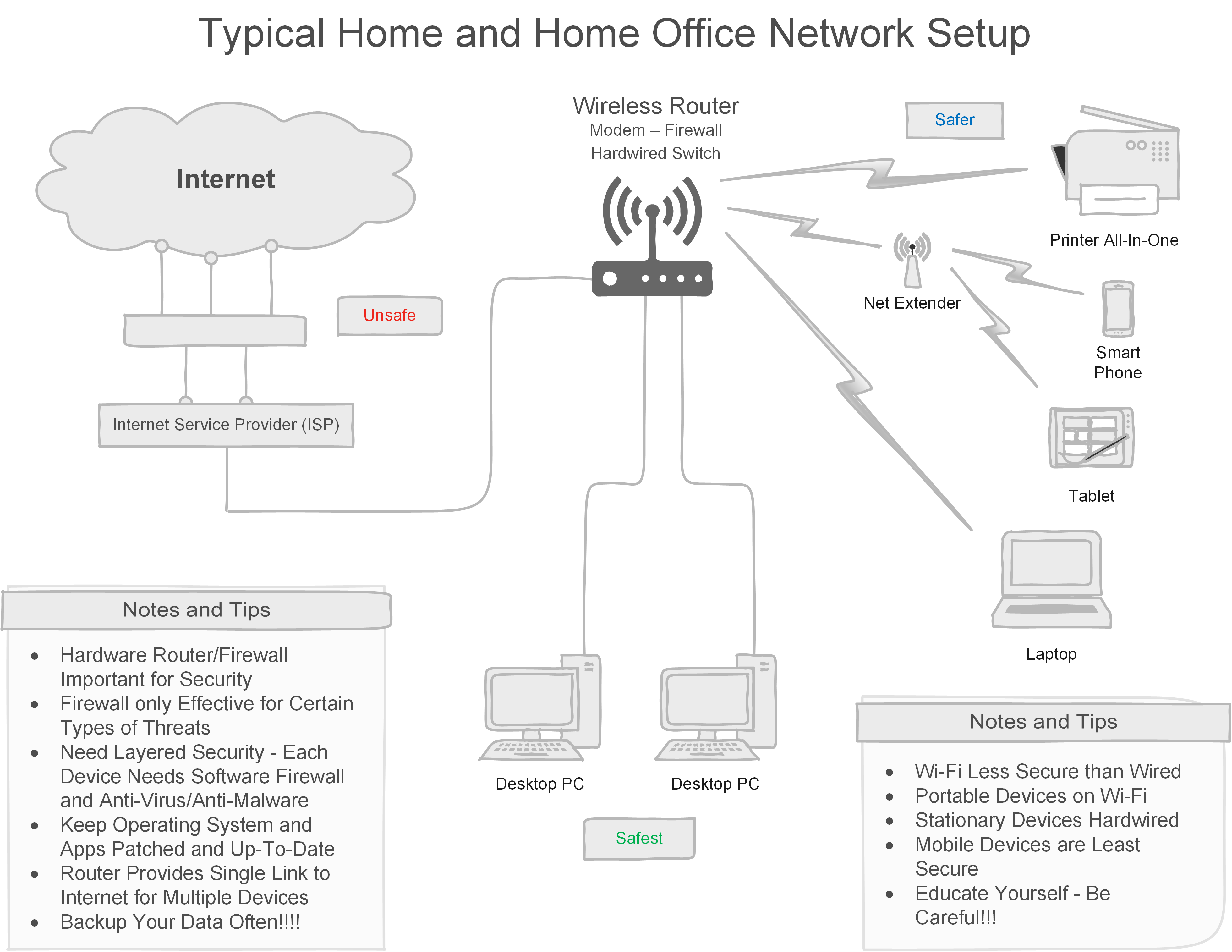
How to Secure a Wireless Network for Home Offices: Ironclad Tips
To secure a wireless network for home offices, change the default router password and enable WPA3 encryption. Regularly update the router’s firmware to protect against vulnerabilities. How to Secure a Wireless Network for Home Offices:In today’s digital age, securing your wireless network is essential, especially for home offices. With sensitive data often transmitted over Wi-Fi,
-

Best Practices for Ethical Hacking in Cybersecurity: Expert Tips
Best practices for ethical hacking in cybersecurity include obtaining proper authorization and maintaining strict confidentiality. Ethical hackers should follow a code of ethics and continuously update their skills. Ethical hacking plays a crucial role in identifying and rectifying security vulnerabilities in systems. Authorized professionals, known as ethical hackers, simulate cyber-attacks to uncover weaknesses before malicious
-
Ethical Hacking Tools for Penetration Testing: Top 10 Must-Haves
Ethical hacking tools are essential for penetration testing. They help identify vulnerabilities in systems. Ethical Hacking Tools for Penetration Testing:Penetration testing involves simulating cyberattacks to uncover security weaknesses. Ethical hacking tools streamline this process, providing security professionals with the means to test and secure their systems effectively. Popular tools include Nmap, Wireshark, and Metasploit, each
-

Ethical Hacking Techniques for Network Security: Ultimate Guide
Ethical hacking techniques identify and fix vulnerabilities in network security. These methods help protect sensitive information from cyber threats. Ethical Hacking Techniques for Network Security:Ethical hacking, often called penetration testing, plays a crucial role in network security. It involves simulating cyber attacks to identify and remedy security flaws. Ethical hackers use various techniques such as
-

Best Ethical Hacking Certifications for Beginners: Top Picks
The best ethical hacking certifications for beginners are Certified Ethical Hacker (CEH) and CompTIA Security+. Both certifications provide a solid foundation in cybersecurity. Ethical hacking certifications are essential for aspiring cybersecurity professionals. They offer structured learning paths and validate your skills. The Certified Ethical Hacker (CEH) is renowned for its comprehensive coverage of hacking techniques.
