A Cybersecurity Risk Assessment evaluates potential threats to an organization’s information systems. It identifies vulnerabilities and assesses their impact on data security.
What is a Cybersecurity Risk Assessment:Cybersecurity is a growing concern for businesses of all sizes. Organizations face numerous threats, including data breaches, malware, and insider threats. A Cybersecurity Risk Assessment is crucial in understanding these risks. It provides a structured approach to identify, evaluate, and prioritize potential vulnerabilities.
By assessing risks, companies can develop effective strategies to mitigate them. This proactive measure not only protects sensitive data but also ensures regulatory compliance. A thorough assessment empowers organizations to allocate resources wisely and improve their overall security posture. Investing in a robust risk assessment can save time and resources in the long run.
Introduction To Cybersecurity Risk Assessment
A cybersecurity risk assessment is a crucial process. It helps organizations identify and manage potential security threats. By evaluating risks, businesses can protect their data and systems effectively.
This assessment is essential for creating a secure environment. It helps in understanding vulnerabilities and their potential impact. Organizations can prioritize their resources better with this knowledge.
The Importance Of Identifying Threats
Identifying threats is vital for any organization. Understanding risks allows companies to:
- Protect sensitive information.
- Prevent data breaches.
- Ensure compliance with regulations.
- Build trust with customers.
Failure to identify threats can lead to severe consequences. Organizations may face financial losses, legal issues, and reputational damage.
Regular assessments keep security measures up to date. They help adapt to new threats in the ever-evolving digital landscape.
Key Components Of An Assessment
Cybersecurity risk assessments have several key components:
- Asset Identification: Recognize critical assets such as data and hardware.
- Threat Analysis: Evaluate potential threats to these assets.
- Vulnerability Assessment: Identify weaknesses in systems.
- Impact Analysis: Assess the potential damage from threats.
- Risk Evaluation: Determine the likelihood and impact of risks.
Each component plays a significant role in the assessment process. Together, they help create a comprehensive risk profile for the organization.
| Component | Description |
|---|---|
| Asset Identification | Identify valuable data and resources. |
| Threat Analysis | Examine potential threats to assets. |
| Vulnerability Assessment | Spot weaknesses in systems and processes. |
| Impact Analysis | Evaluate damage from possible threats. |
| Risk Evaluation | Assess likelihood and impact of risks. |
Types Of Cybersecurity Risks
Understanding the types of cybersecurity risks is crucial for any organization. Different risks can affect systems, data, and users. Identifying these risks helps in implementing effective security measures.
Common Cyber Threats
Common cyber threats include various attacks that target networks and devices. Here are some prevalent ones:
- Malware: Malicious software that can damage systems.
- Phishing: Fraudulent emails that trick users into sharing sensitive data.
- Ransomware: A type of malware that locks files until a ransom is paid.
- DDoS Attacks: Overloading a network with traffic to disrupt services.
- Insider Threats: Current or former employees who misuse access to data.
Emerging Risks In The Digital Age
The digital age brings new challenges in cybersecurity. Here are some emerging risks:
- IoT Vulnerabilities: Devices connected to the internet can be exploited.
- Cloud Security Issues: Storing data in the cloud raises concerns about breaches.
- AI-Powered Attacks: Cybercriminals use artificial intelligence for more sophisticated attacks.
- Supply Chain Attacks: Targeting third-party vendors to access larger networks.
| Risk Type | Description |
|---|---|
| Malware | Software designed to harm or exploit devices. |
| Phishing | Tricks users into providing personal information. |
| Ransomware | Files are locked until a ransom is paid. |
| DDoS | Disrupts services by overwhelming networks. |
| Insider Threats | Employees misuse their access to sensitive data. |
| IoT Risks | Connected devices can be hacked. |
| Cloud Security | Data stored online can be vulnerable to breaches. |
| AI Attacks | AI techniques used for advanced cyberattacks. |
| Supply Chain | Third-party vendors can be exploited to attack main networks. |
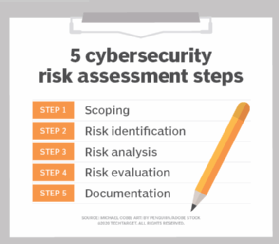
Steps In Conducting A Risk Assessment
Conducting a cybersecurity risk assessment is crucial. It helps identify potential threats to your organization. Following specific steps ensures a thorough evaluation. Let’s explore these steps in detail.
Identifying Assets
First, identify your organization’s assets. Assets can include:
- Data: Customer information, financial records
- Hardware: Computers, servers, and routers
- Software: Applications, operating systems
- Personnel: Employees and their roles
Use a table to list each asset with its value:
| Asset | Value |
|---|---|
| Customer Data | High |
| Company Servers | Medium |
| Software Licenses | Medium |
Determining Threats And Vulnerabilities
Next, identify threats and vulnerabilities. Consider the following:
- Threats: Cyberattacks, natural disasters
- Vulnerabilities: Outdated software, weak passwords
Use an ordered list to categorize them:
- Malware attacks
- Phishing attempts
- Insider threats
Assessing Impact And Likelihood
Finally, assess the impact and likelihood of each threat. Ask these questions:
- What would happen if the threat occurs?
- How likely is this threat?
Use a simple table to categorize risks:
| Threat | Impact | Likelihood |
|---|---|---|
| Data Breach | High | Medium |
| Ransomware Attack | Critical | High |
| Insider Threat | Medium | Low |
Credit: www.techtarget.com
Tools And Techniques For Risk Analysis
Cybersecurity risk assessments rely on various tools and techniques. These help organizations identify and manage risks effectively. Proper analysis enhances security measures, reduces vulnerabilities, and protects sensitive data.
Automated Assessment Solutions
Automated tools streamline the risk assessment process. They save time and increase accuracy. Here are some common automated assessment solutions:
- Vulnerability Scanners: Identify weaknesses in systems.
- Threat Intelligence Platforms: Gather data on potential threats.
- Security Information and Event Management (SIEM): Monitor and analyze security events.
- Compliance Management Tools: Ensure adherence to regulations.
These tools provide quick insights. They help prioritize risks based on severity. Organizations can address critical issues first.
Manual Assessment Strategies
Manual assessments require human expertise. Teams evaluate risks through various methods. Below are key strategies:
- Interviews: Talk to staff about security practices.
- Document Reviews: Examine policies and procedures.
- Risk Workshops: Collaborate with teams to identify risks.
- Scenario Analysis: Consider potential attack scenarios.
Manual strategies offer in-depth understanding. They capture nuances automated tools might miss. Combining both methods enhances overall risk analysis.
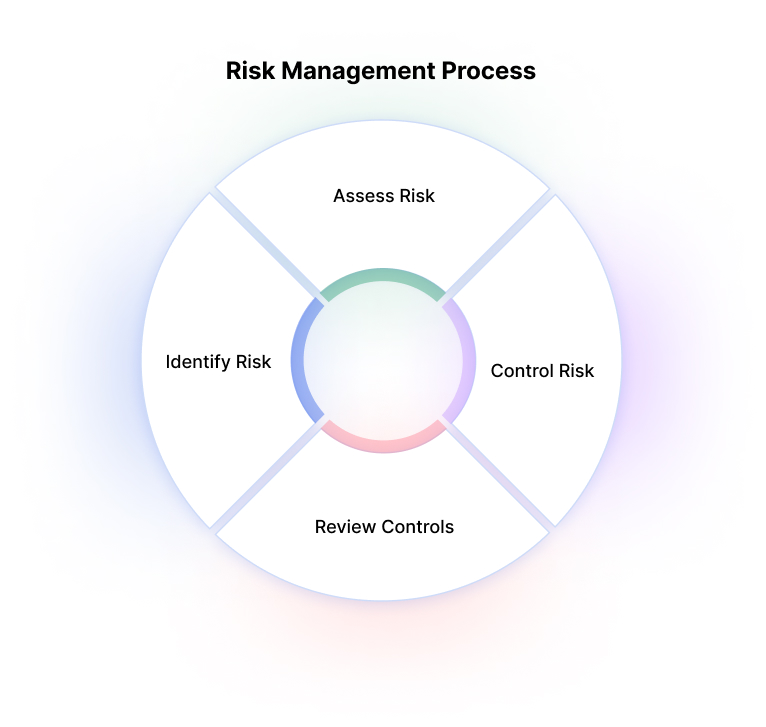
Interpreting Risk Assessment Outcomes
Understanding the results of a cybersecurity risk assessment is crucial. It helps organizations identify, evaluate, and manage potential threats. Clear interpretation guides decision-making and prioritizes actions.
Understanding The Risk Matrix
A risk matrix visually displays the level of risk. It combines the likelihood of a threat and the impact it may have. The matrix typically consists of rows and columns.
| Likelihood | Impact |
|---|---|
| Low | Minor |
| Medium | Moderate |
| High | Severe |
Each cell in the matrix represents a different risk level:
- Low Risk: Minimal action needed.
- Medium Risk: Monitor closely.
- High Risk: Immediate action required.
Prioritizing Risks For Action
After assessing risks, prioritize them based on their scores. Focus on high-risk items first. Use the following steps for effective prioritization:
- List all identified risks.
- Assign scores based on likelihood and impact.
- Rank risks from highest to lowest score.
- Create an action plan for high-ranking risks.
Regularly review and update this list. This ensures your cybersecurity measures stay effective. Always aim for continuous improvement in risk management.
Best Practices For An Effective Assessment
Conducting a cybersecurity risk assessment is vital for protecting your organization. Following best practices helps ensure the assessment is thorough and effective. Here are key practices to consider.
Regular Updates To Risk Profiles
Cyber threats evolve constantly. Regular updates to risk profiles keep your organization safe. Here are steps to maintain updated risk profiles:
- Review risk profiles at least quarterly.
- Incorporate new threat intelligence.
- Assess changes in technology and infrastructure.
- Document lessons learned from incidents.
Updating profiles allows your team to:
| Benefit | Description |
|---|---|
| Identify New Risks | Spot emerging threats quickly. |
| Improve Response Time | Enhance preparedness for incidents. |
| Allocate Resources Effectively | Focus on high-risk areas. |
Involving The Right Stakeholders
Engaging the right stakeholders is crucial. Collaboration leads to better risk assessment. Include the following groups:
- IT Security Team: They provide technical insights.
- Management: They offer strategic direction.
- Legal Advisors: They ensure compliance with laws.
- Employees: They help identify potential risks.
Involvement fosters a culture of security. All team members should understand their roles. This teamwork enhances the effectiveness of the assessment.
Challenges In Cybersecurity Risk Assessments
Cybersecurity risk assessments face many challenges. These challenges can complicate the process. Understanding them helps organizations better prepare.
Dealing With Complex Infrastructures
Modern organizations often have complicated IT setups. These setups can include:
- Multiple servers
- Cloud services
- Mobile devices
- Third-party applications
Each component introduces unique vulnerabilities. Identifying risks across these layers is tough. A clear view of the entire infrastructure is essential.
Organizations may struggle to:
- Map their assets accurately
- Track data flows
- Evaluate third-party risks
Overcoming Compliance Hurdles
Regulatory compliance adds another layer of complexity. Organizations must follow laws like:
- GDPR
- HIPAA
- PCI DSS
Each regulation has specific requirements. Failing to meet them can lead to severe penalties.
Common compliance challenges include:
| Challenge | Description |
|---|---|
| Lack of Awareness | Many staff members do not understand compliance rules. |
| Documentation Issues | Keeping proper records can be difficult. |
| Frequent Changes | Regulations often change, requiring updates to policies. |
Staying compliant while assessing risks is crucial. Organizations must balance security with regulatory needs.
Credit: www.imperva.com
Case Studies: Learning From Past Breaches
Analyzing past breaches helps organizations understand risks. Learning from these events can improve cybersecurity strategies. By studying real incidents, businesses can avoid similar mistakes.
Analyzing High-profile Cyber Attacks
High-profile cyber attacks teach valuable lessons. Here are a few notable cases:
| Company | Year | Type of Attack | Impact |
|---|---|---|---|
| Target | 2013 | Data Breach | 40 million credit cards compromised |
| Equifax | 2017 | Data Breach | 147 million personal records stolen |
| Yahoo | 2013-2014 | Data Breach | 3 billion accounts hacked |
These attacks highlight the importance of cybersecurity assessments. Understanding the attack methods helps in preventing similar issues.
Lessons Learned And Applied Strategies
Each attack provides crucial lessons. Companies can adopt strategies to enhance security.
- Regular Audits: Conduct frequent security audits.
- Employee Training: Train staff on security protocols.
- Incident Response Plans: Develop clear response plans for breaches.
- Data Encryption: Encrypt sensitive data to protect it.
Implementing these strategies can significantly reduce risks. Companies should always stay updated on cybersecurity trends. Learning from past breaches creates a safer digital environment.
Future Of Cybersecurity Risk Assessments
The future of cybersecurity risk assessments is evolving rapidly. Organizations face new challenges daily. Adopting advanced tools is essential for staying ahead. Understanding these changes is crucial for protection.
Incorporating Ai And Machine Learning
Artificial Intelligence (AI) and Machine Learning (ML) play vital roles in cybersecurity. These technologies analyze vast amounts of data quickly. They identify patterns and predict threats.
- Enhanced Threat Detection: AI algorithms spot unusual activities.
- Automated Responses: ML can trigger immediate actions.
- Continuous Learning: Systems adapt as new threats emerge.
Using AI and ML improves risk assessments. Organizations can focus on critical areas. They save time and resources, making them more efficient.
Adapting To Evolving Cyber Threat Landscapes
The cyber threat landscape changes constantly. New types of attacks emerge regularly. Risk assessments must adapt to these shifts.
- Regular Updates: Review assessments frequently.
- Threat Intelligence: Stay informed about new threats.
- Collaboration: Work with cybersecurity experts.
Organizations should prioritize flexibility in their strategies. Agile approaches help them respond to new risks swiftly. Emphasizing ongoing training is crucial for all staff. Awareness leads to a stronger defense.
| Key Strategies | Description |
|---|---|
| AI Integration | Utilize AI for faster threat detection. |
| Frequent Reviews | Conduct regular assessments to stay updated. |
| Collaboration | Engage with cybersecurity professionals. |

Credit: www.linkedin.com
Frequently Asked Questions
What Is The Purpose Of A Cybersecurity Risk Assessment?
A cybersecurity risk assessment identifies vulnerabilities in an organization’s systems. Its purpose is to evaluate potential threats and their impact. This assessment helps prioritize security measures and allocate resources effectively. Ultimately, it aims to protect sensitive data and maintain operational integrity.
Who Should Conduct A Cybersecurity Risk Assessment?
A cybersecurity risk assessment should be conducted by trained professionals. This includes IT security teams, external consultants, or auditors. They have the expertise to identify risks accurately. Engaging multiple perspectives ensures a comprehensive evaluation of the organization’s security posture.
How Often Should You Perform A Risk Assessment?
Organizations should perform a cybersecurity risk assessment annually. However, significant changes in technology, personnel, or regulations may require more frequent evaluations. Regular assessments ensure that security measures remain effective against evolving threats. Staying proactive helps organizations maintain robust cybersecurity defenses.
What Are The Key Components Of A Risk Assessment?
Key components of a cybersecurity risk assessment include asset identification, threat analysis, and vulnerability assessment. Organizations must evaluate potential impacts and likelihood of risks. Additionally, risk prioritization and mitigation strategies are crucial. These components create a comprehensive understanding of the security landscape.
Conclusion
A cybersecurity risk assessment is essential for protecting your organization. It identifies vulnerabilities and helps prioritize security measures. Regular assessments ensure you stay ahead of potential threats. By implementing a robust risk assessment strategy, you can safeguard your assets and maintain trust with clients.
Stay proactive to enhance your cybersecurity posture effectively.




Leave a Reply